- How can I see what ports are open on my machine?
- 10 Answers 10
- nmap (install)
- How to Check Open Ports in Linux
- What Is a Listening Port?
- How to Check Open Ports in Linux?
- Check Ports via lsof Command
- Check Ports via netstat Command
- Check Ports via ss Command
- Check Ports via nmap Command
- Check Ports via nc Command
- How to Check (Scan) for Open Ports in Linux
- Introduction
- What is Open Port?
- Check Open Ports with nmap
- Check Open Ports with netcat
- Check Open Ports using Bash Pseudo Device
- Conclusion
How can I see what ports are open on my machine?
I would like to see what ports are open on my machine, e.g. what ports my machine is listening on. E.g. port 80 if I have installed a web server, and so on. Is there any command for this?
10 Answers 10
If the netstat command is not available, install it with:
sudo apt install net-tools -l already filters for listening. grep LISTEN won’t help beyond hiding 2 lines of header information.
-t : tcp, -l : listening socket, -p : show pid and program name, -n : print 127.0.0.1:80 instead of localhost:http . Reference: linux.die.net/man/8/netstat
The expanded command is sudo netstat —tcp —listening —programs —numeric . There’s no need to use grep unless you want to eliminate column headers.
nmap (install)
Nmap («Network Mapper») is a free and open source utility for network exploration or security auditing.
Use nmap 192.168.1.33 for internal PC or nmap external IP address .
More information man nmap .
Zenmap is the official GUI frontend.
Remember that there is a difference between nmap localhost and nmap 192.168.0.3 (or what ever you machine IP is)
I think netstat is a better answer to this. netstat will list what the system is listening on directly, and without using an additional application or doing unnecessary calls over localhost or thought the network.
This is stupid. If you have access to the computer, just use netstat -ln . You’ll instantly see all the open ports.
nmap localhost didn’t find services that were bound only to localhost. For example, I run influxd with bind-address:localhost:8086 . That didn’t show up in sudo nmap localhost , but did show up in sudo netstat -tulpn .
Other good ways to find out what ports are listenting and what your firewall rules are:
To list open ports use the netstat command.
$ sudo netstat -tulpn | grep LISTEN tcp 0 0 127.0.0.1:53 0.0.0.0:* LISTEN 5452/dnsmasq tcp 0 0 127.0.0.1:631 0.0.0.0:* LISTEN 1037/cupsd tcp6 0 0 ::1:631 . * LISTEN 1037/cupsd In the above example three services are bound to the loopback address.
IPv4 services bound to the loopback address «127.0.0.1» are only available on the local machine. The equivalent loopback address for IPv6 is «::1». The IPv4 address «0.0.0.0» means «any IP address», which would mean that other machines could potentially connect to any of the locally configured network interfaces on the specific port.
Another method is to use the lsof command:
$ sudo lsof -nP -i | grep LISTEN cupsd 1037 root 9u IPv6 11276 0t0 TCP [::1]:631 (LISTEN) cupsd 1037 root 10u IPv4 11277 0t0 TCP 127.0.0.1:631 (LISTEN) dnsmasq 5452 nobody 5u IPv4 212707 0t0 TCP 127.0.0.1:53 (LISTEN) For more details see man netstat or man lsof .
How to Check Open Ports in Linux
Network ports are standardized number identifiers that allow devices to use one IP address to handle multiple network requests simultaneously. Since there are 65535 port numbers, keeping a record of which ports are in use can be challenging.
This article will teach you how to check for open listening ports on a Linux system using five popular networking tools.
What Is a Listening Port?
Applications and services use listening ports to listen for incoming network requests. Each listening port is tied to an IP address and a communication protocol such as TCP or UDP.
Depending on the network setup, listening ports can be open or closed.
- Open ports accept outside connections using the correct protocol.
- Closed ports do not accept all the connections. They communicate with a predetermined outside service or application while a firewall blocks other attempted connections.
One listening port tied can host only one service. For instance, if there is a web server on the system that already uses port 80, any other installed web server will have to use a different, non-default port number.
How to Check Open Ports in Linux?
Linux users can check open ports using multiple available networking tools. Each tool displays the same results, but the output format and the amount of information vary.
The following sections provide instructions for checking open ports using lsof, netstat, ss, Nmap, and netcat utilities.
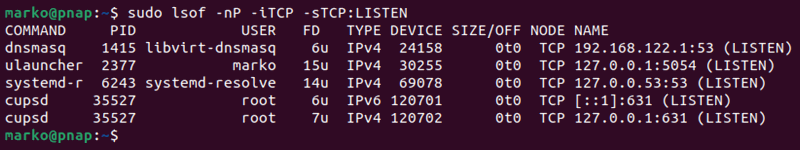
Check Ports via lsof Command
The lsof command allows users to list the programs that utilize listening ports and daemons that maintain active network connections.
Use the lsof command to:
sudo lsof -nP -iTCP -sTCP:LISTENThe command outputs a list of the connections that use the TCP protocol.
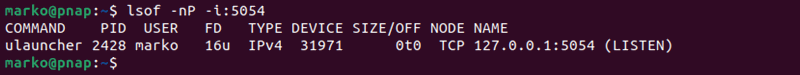
For example, to check if port 5054 is in use, type:
If the port is free, the command shows no output. If an application is using the port, the output shows its details:
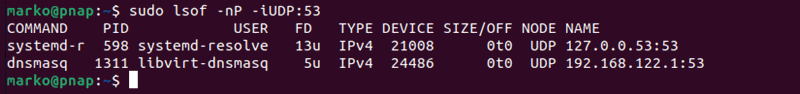
For example, to check if the UDP port 53 is open, type:
The output shows if an application already uses the port.
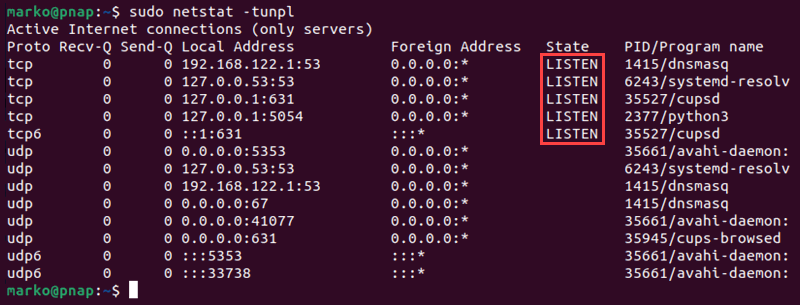
Check Ports via netstat Command
The netstat command provides a network activity overview and statistics. Use the command below to display the listening ports on the system with netstat :
The command uses five command arguments:
- -t — Queries the command for TCP ports.
- -u — Queries for UDP ports.
- -n — Avoids DNS lookup and shows only IP addresses to speed up the process.
- -p — Displays the process ID and the name of the program using the port.
- -l — Outputs listening ports.
Identify the listening ports/sockets by checking the State column and looking for the label LISTENING .
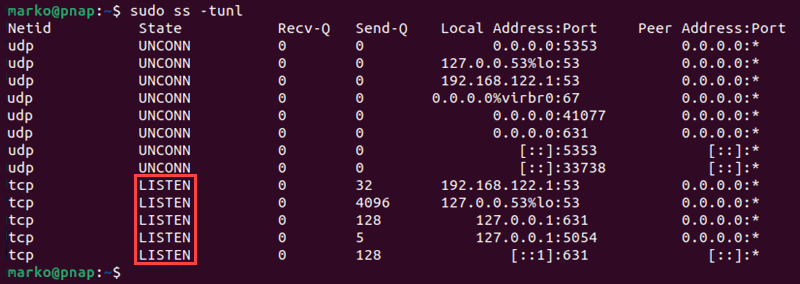
Check Ports via ss Command
The ss command is a faster and easier-to-use version of the obsolete netstat command. It uses the same options as netstat , but provides more statistics in the output.
The following command scans TCP and UDP ports for listening sockets and displays them in a list:
The listening ports/sockets are marked as LISTEN in the State column.
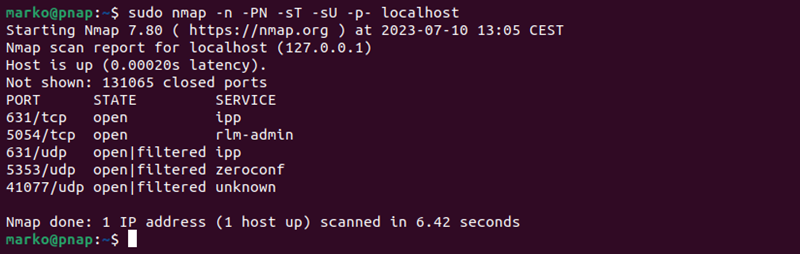
Check Ports via nmap Command
The Nmap utility allows users to scan for open ports on local and remote systems. Execute the command below to scan for all open TCP and UDP ports on the local system:
sudo nmap -n -PN -sT -sU -p- localhost The following are the nmap options used in the example.
- -n — Skips DNS resolution.
- -PN — Skips the discovery phase.
- -sT and -sU — Tell netstat to scan TCP and UDP ports, respectively.
- -p- — Scans all the ports.
The output lists the open ports alongside the services that use them.
Note: If you want to scan a port range, specify it with the -p option. For example, to scan only the UDP ports from 1 to 1023, type:
sudo nmap -p U:1-1023 localhost
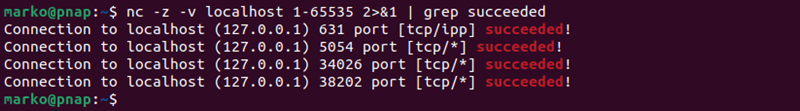
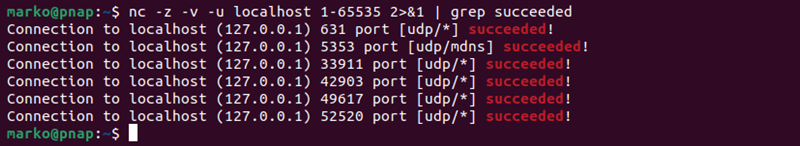
Check Ports via nc Command
The nc command in Linux allows users to control the netcat utility. netcat can scan the ports on local and remote systems and provide information on whether the ports are open, closed, or filtered by a firewall.
Note: In CentOS, RHEL, and Debian the natcat command is ncat .
Scan all the ports on the local system by typing:
The -z flag enables the zero-I/O mode used for scanning, while the -v option tells netcat to produce verbose output.
When the command is executed, netcat attempts to connect to all the ports and reports on the success for each port. Scanning many ports at once produces an extensive output.
To show only the ports where the connection succeeded, i.e., the open ports, use the 2>$1 expression to redirect the output. Then, pipe the expression to the grep command and search for the word succeeded .
nc -z -v localhost 1-65535 2>&1 | grep succeededBy default, netcat scans TCP ports. To check UDP ports, add the -u option:
nc -z -v -u localhost 1-65535 2>&1 | grep succeededAfter reading this article, you should know how to use the five popular Linux utilities to check for open ports. Knowing which ports are open on your system may help you detect an intrusion or troubleshoot network-related issues.
How to Check (Scan) for Open Ports in Linux
In this tutorial, we will discuss many methods for determining which ports on your Linux system are available to the outside world.
Introduction
One of the first things to check when troubleshooting network connectivity issues or establishing a firewall is whether ports are truly open on your machine.
In this tutorial, we will discuss many methods for determining which ports on your Linux system are available to the outside world.
What is Open Port?
A program that listens on a network port is known as a listening port. You may retrieve a list of your system’s listening ports by using tools like ss , netstat , or lsof to query the network stack. Using a firewall, each listening port can be opened or blocked (filtered).
A network port that admits incoming packets from faraway destinations is known as an open port.
For instance, if your web server listens on ports 80 and 443 and those ports are open on your firewall, anyone (excluding blocked ips) can use his browser to view websites housed on your web server. Both ports 80 and 443 are open in this scenario.
Open ports can be a security issue since attackers can use them to exploit vulnerabilities or carry out other types of attacks. All other ports should be closed and just the ports required for your application’s operation should be exposed.
Check Open Ports with nmap
Nmap is a network scanning program capable of scanning both single hosts and big networks. It’s mostly used for penetration testing and security assessments.
When it comes to port scanning, nmap should be your first choice if it is available. Nmap can determine the Mac address, OS type, kernel versions, and much more in addition to port scanning.
Which ports are listening for TCP connections from the network can be determined by using the following command from the console:
The -sT option instructs nmap to scan for TCP ports, whereas the -p- option instructs it to scan for all 65535 ports. If the -p- option is not specified, nmap will only scan the 1000 most popular ports.
Output Starting Nmap 7.60 ( https://nmap.org ) at 2019-07-09 23:10 CEST Nmap scan report for 10.10.8.8 Host is up (0.0012s latency). Not shown: 998 closed ports PORT STATE SERVICE 22/tcp open ssh 80/tcp open http MAC Address: 08:00:27:05:49:23 (Oracle VirtualBox virtual NIC) Nmap done: 1 IP address (1 host up) scanned in 0.41 seconds Only ports 22 , 80 , and 8069 are open on the target system, according to the output.
Instead of -sT , use -sU to scan for UDP ports:
Visit the nmap man page for more information and to learn about all of this tool’s other useful features.
Check Open Ports with netcat
Netcat (or nc ) is a command-line utility that uses the TCP or UDP protocols to read and write data across network connections.
Netcat can scan a single port or a range of ports.
To search for open TCP ports on a distant system with IP address 10.10.8.8 in the range 20-80 , for example, execute the command:
The -z option instructs nc to scan only for open ports and not transfer any data, whereas the -v option provides more detailed information.
This is what the output will look like:
Output The -z option instructs nc to scan only for open ports and not transfer any data, whereas the -v option provides more detailed information. This is what the final product will look like: If you just want the lines with open ports written on the screen, use the grep command to filter the results.
nc -z -v 10.10.8.8 20-80 2>&1 | grep succeeded Output Connection to 10.10.8.8 22 port [tcp/ssh] succeeded! Connection to 10.10.8.8 80 port [tcp/http] succeeded! Pass the -u argument to the nc command to scan for UDP ports:
nc -z -v -u 10.10.8.8 20-80 2>&1 | grep succeeded Check Open Ports using Bash Pseudo Device
The Bash shell /dev/tcp/.. or /dev/udp/.. pseudo-device can also be used to determine whether a port is open or closed.
Bash will open a TCP or UDP connection to the specified host on the specified port when a command is run on a /dev/$PROTOCOL/$HOST/$IP pseudo-device.
The if..else statement below will check if port 443 on kernel.org is open:
if timeout 5 bash -c '/dev/null' then echo "Port is open" else echo "Port is closed" fi What is the purpose of the code above?
Because the default timeout when connecting to a port via a pseudo-device is so long, we’re utilizing the timeout command to kill the test command after 5 seconds. The test command will return true if the connection to kernel.org port 443 is established.
Use the for loop to check for a port range:
for PORT in ; do timeout 1 bash -c "/dev/null" && echo "port $PORT is open" done You will get an output like below:
Output port 22 is open port 80 is open Conclusion
We’ve taught you how to scan for open ports with a variety of tools. You can also check for open ports using other utilities and methods, such as the Python socket module, curl , telnet , or wget .
If you have any queries, please leave a comment below and we’ll be happy to respond to them.