- How to find ports opened by process ID in Linux?
- -p (Linux):
- How to Check for Listening Ports in Linux (Ports in use)
- What is Listening Port #
- Check Listening Ports with netstat #
- Check Listening Ports with ss #
- Check Listening Ports with lsof #
- Conclusion #
- 4 Ways to Find Out What Ports Are Listening in Linux
- 1. Using Netstat Command
- 2. Using ss Command
- 3. Using Nmap Command
- 4. Using lsof Command
How to find ports opened by process ID in Linux?
Hmm..I don’t seem to have the —all and —program options. I’m using OSX. Brew doesn’t seem to have a formula for it either.
-n will dramatically speed things up by not resolving hostnames. netsta -tupan is a good default command all and easy to remember.
You can use the command below:
As a side note, netstat -ao will read the /proc/PID/tcp etc to see the ports opened by the process. This means that its reading information supplied by the system (the linux KERNEL), and is in no way directly looking on the network interface or other means. Same goes for lsof.
If you are doing this as a security measure, you failed. You should never (NEVER EVER) trust the output of netstat, even if you are 100% sure you are in fact running a real netstat program (as opposed to a trojaned version) or any other program that reads the /proc filesystem. Some people seem to think that netstat, ls, ps or any other of the standard unix tools do some sort of magic and poll information from the sources, the truth is all of them rely on the /proc filesystem to get all of their data, which can be easily subverted by a rootkit or hypervisor.
If you’re dealing with a rootkitted system or a compromised hypervisor, you can’t trust anything, including something that purports to look directly at the network interface.
You can use the netstat command line tool with the -p command line argument:
-p (Linux):
Process: Show which processes are using which sockets (similar to -b under Windows). You must be root to do this.
To display all ports open by a process with id $PID :
In some embedded devices or with old version of Linux, the problem is netstat do not have —process or -p options available.
The following script shows process with its IP and port, you must be root.
#!/bin/bash for protocol in tcp udp ; do #echo "protocol $protocol" ; for ipportinode in `cat /proc/net/$ | awk '/.*:.*:.*/'` ; do #echo "#ipportinode=$ipportinode" inode=`echo "$ipportinode" | cut -d"|" -f3` ; if [ "#$inode" = "#" ] ; then continue ; fi lspid=`ls -l /proc/*/fd/* 2>/dev/null | grep "socket:\[$inode\]" 2>/dev/null` ; pid=`echo "lspid=$lspid" | awk 'BEGIN /socket/'` ; if [ "#$pid" = "#" ] ; then continue ; fi exefile=`ls -l /proc/$pid/exe | awk 'BEGIN ">/->/'` #echo "$protocol|$pid|$ipportinode" echo "$protocol|$pid|$ipportinode|$exefile" | awk ' BEGIN function iphex2dec(ipport) < ret=sprintf("%d.%d.%d.%d: %d","0x"substr(ipport,1,2),"0x"substr(ipport,3,2), "0x"substr(ipport,5,2),"0x"substr(ipport,7,2),"0x"substr(ipport,10,4)) ; if( ret == "0.0.0.0:0" ) #compatibility others awk versions < ret= strtonum("0x"substr(ipport,1,2)) ; ret=ret "." strtonum("0x"substr(ipport,3,2)) ; ret=ret "." strtonum("0x"substr(ipport,5,2)) ; ret=ret "." strtonum("0x"substr(ipport,7,2)) ; ret=ret ":" strtonum("0x"substr(ipport,10)) ; >return ret ; > < print $1" pid:"$2" local="iphex2dec($3)" remote="iphex2dec($4)" inode:"$5" exe=" $6 ; >' ; #ls -l /proc/$pid/exe ; done ; done tcp pid:1454 local=1.0.0.127:5939 remote=0.0.0.0:0 inode:13955 exe=/opt/teamviewer/tv_bin/teamviewerd tcp pid:1468 local=1.1.0.127:53 remote=0.0.0.0:0 inode:12757 exe=/usr/sbin/dnsmasq tcp pid:1292 local=0.0.0.0:22 remote=0.0.0.0:0 inode:12599 exe=/usr/sbin/sshd tcp pid:4361 local=1.0.0.127:631 remote=0.0.0.0:0 inode:30576 exe=/usr/sbin/cupsd tcp pid:1375 local=1.0.0.127:5432 remote=0.0.0.0:0 inode:12650 exe=/usr/lib/postgresql/9.3/bin/postgres With ls you can know the process route.
The fuser command says that the process is: 2054
I’ve added IPv6 support and made a few fixes. Additionally on my system the octets of the IP address are reversed. Dependencies are only to posix shell, awk and cut.
My Version can be found on Github
#!/bin/sh # prints all open ports from /proc/net/* # # for pretty output (if available) start with # ./linux-get-programm-to-port.sh | column -t -s $'\t' #set -x ip4hex2dec () < local ip4_1octet="0x$" local ip4_2octet="$" ip4_2octet="0x$" local ip4_3octet="$" ip4_3octet="0x$" local ip4_4octet="$" ip4_4octet="0x$" local ip4_port="0x$" # if not used inverse #printf "%d.%d.%d.%d:%d" "$ip4_1octet" "$ip4_2octet" "$ip4_3octet" "$ip4_4octet" "$ip4_port" printf "%d.%d.%d.%d:%d" "$ip4_4octet" "$ip4_3octet" "$ip4_2octet" "$ip4_1octet" "$ip4_port" > # reoder bytes, byte4 is byte1 byte2 is byte3 . reorderByte() < if [ $-ne 8 ]; then echo "missuse of function reorderByte"; exit; fi local byte1="$" local byte2="$" byte2="$" local byte3="$" byte3="$" local byte4="$" echo "$byte4$byte3:$byte2$byte1" > # on normal intel platform the byte order of the ipv6 address in /proc/net/*6 has to be reordered. ip6hex2dec()< local ip_str="$" local ip6_port="0x$" local ipv6="$(reorderByte $)" local shiftmask="$" ipv6="$ipv6:$(reorderByte $)" shiftmask="$" ipv6="$ipv6:$(reorderByte $)" ipv6="$ipv6:$(reorderByte $)" ipv6=$(echo $ipv6 | awk '< gsub(/(:0|^0)/, ":"); sub(/(:0)+:/, "::");print>') printf "%s:%d" "$ipv6" "$ip6_port" > for protocol in tcp tcp6 udp udp6 raw raw6; do #echo "protocol $protocol" ; for ipportinode in `cat /proc/net/$protocol | awk '/.*:.*:.*/'` ; do #echo "#ipportinode=$ipportinode" inode=$ if [ "#$inode" = "#" ] ; then continue ; fi lspid=`ls -l /proc/*/fd/* 2>/dev/null | grep "socket:\[$inode\]" 2>/dev/null` ; pids=`echo "$lspid" | awk 'BEGIN /socket/ END>'` ; # removes duplicats for this pid #echo "#lspid:$lspid #pids:$pids" for pid in $pids; do if [ "#$pid" = "#" ] ; then continue ; fi exefile=`ls -l /proc/$pid/exe | awk 'BEGIN ">/->/'`; cmdline=`cat /proc/$pid/cmdline` local_adr_hex=$ remote_adr_hex=$ remote_adr_hex=$ if [ "#$" = "#6" ]; then local_adr=$(ip6hex2dec $local_adr_hex) remote_adr=$(ip6hex2dec $remote_adr_hex) else local_adr=$(ip4hex2dec $local_adr_hex) remote_adr=$(ip4hex2dec $remote_adr_hex) fi echo "$protocol pid:$pid \t$local_adr \t$remote_adr \tinode:$inode \t$exefile $cmdline" done done done How to Check for Listening Ports in Linux (Ports in use)
When troubleshooting network connectivity or application-specific issues, one of the first things to check should be what ports are actually in use on your system and which application is listening on a specific port.
This article explains how to use the netstat , ss and lsof commands to find out which services are listening on which ports. The instructions are applicable for all Linux and Unix-based operating systems like macOS.
What is Listening Port #
Network port is identified by its number, the associated IP address, and type of the communication protocol, such as TCP or UDP.
Listening port is a network port on which an application or process listens on, acting as a communication endpoint.
Each listening port can be open or closed (filtered) using a firewall. In general terms, an open port is a network port that accepts incoming packets from remote locations.
You can’t have two services listening to the same port on the same IP address.
For example, if you are running an Apache web server that listens on ports 80 and 443 and you try to install Nginx , the later will fail to start because the HTTP and HTTPS ports are already in use.
Check Listening Ports with netstat #
netstat is a command-line tool that can provide information about network connections.
To list all TCP or UDP ports that are being listened on, including the services using the ports and the socket status use the following command:
The options used in this command have the following meaning:
- -t — Show TCP ports.
- -u — Show UDP ports.
- -n — Show numerical addresses instead of resolving hosts.
- -l — Show only listening ports.
- -p — Show the PID and name of the listener’s process. This information is shown only if you run the command as root or sudo user.
The output will look something like this:
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN 445/sshd tcp 0 0 0.0.0.0:25 0.0.0.0:* LISTEN 929/master tcp6 0 0 . 3306 . * LISTEN 534/mysqld tcp6 0 0 . 80 . * LISTEN 515/apache2 tcp6 0 0 . 22 . * LISTEN 445/sshd tcp6 0 0 . 25 . * LISTEN 929/master tcp6 0 0 . 33060 . * LISTEN 534/mysqld udp 0 0 0.0.0.0:68 0.0.0.0:* 966/dhclient The important columns in our case are:
- Proto — The protocol used by the socket.
- Local Address — The IP Address and port number on which the process listen to.
- PID/Program name — The PID and the name of the process.
If you want to filter the results, use the grep command . For example, to find what process listens on TCP port 22 you would type:
sudo netstat -tnlp | grep :22The output shows that on this machine port 22 is used by the SSH server:
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN 445/sshd tcp6 0 0 . 22 . * LISTEN 445/sshd If the output is empty it means that nothing is listening on the port.
You can also filter the list based on criteria, for example, PID, protocol, state, and so on.
netstat is obsolete and replaced with ss and ip , but still it is of the most used commands to check network connections.
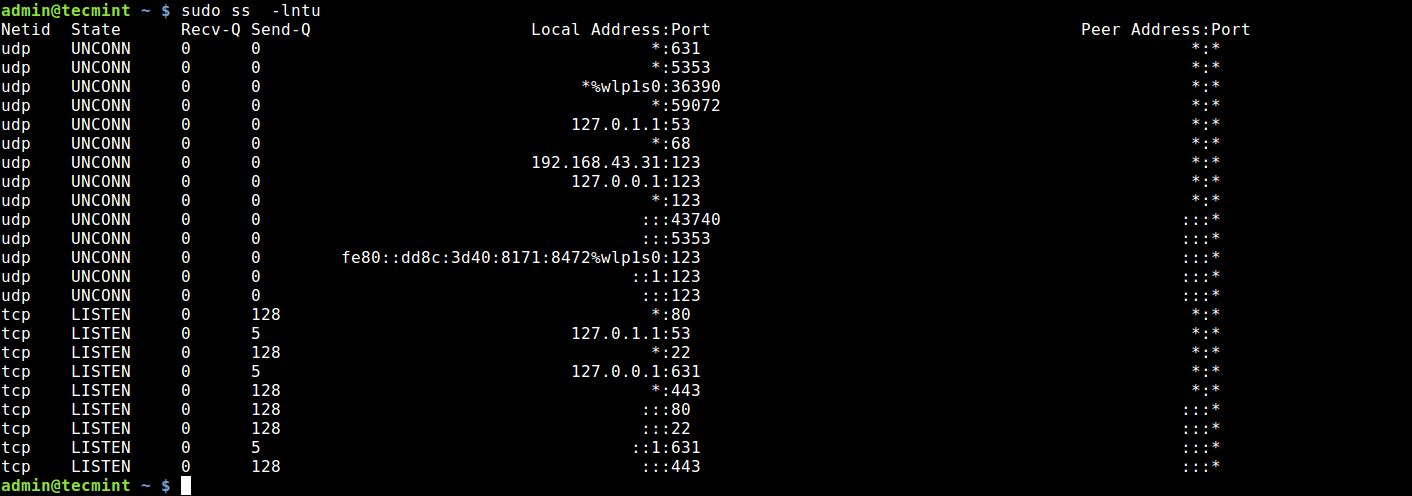
Check Listening Ports with ss #
ss is the new netstat . It lacks some of the netstat features, but exposes more TCP states and it is slightly faster. The command options are mostly the same, so the transition from netstat to ss is not difficult.
To get a list of all listening ports with ss you would type:
The output is almost the same as the one reported by netstat :
State Recv-Q Send-Q Local Address:Port Peer Address:Port LISTEN 0 128 0.0.0.0:22 0.0.0.0:* users:(("sshd",pid=445,fd=3)) LISTEN 0 100 0.0.0.0:25 0.0.0.0:* users:(("master",pid=929,fd=13)) LISTEN 0 128 *:3306 *:* users:(("mysqld",pid=534,fd=30)) LISTEN 0 128 *:80 *:* users:(("apache2",pid=765,fd=4),("apache2",pid=764,fd=4),("apache2",pid=515,fd=4)) LISTEN 0 128 [::]:22 [::]:* users:(("sshd",pid=445,fd=4)) LISTEN 0 100 [::]:25 [::]:* users:(("master",pid=929,fd=14)) LISTEN 0 70 *:33060 *:* users:(("mysqld",pid=534,fd=33)) Check Listening Ports with lsof #
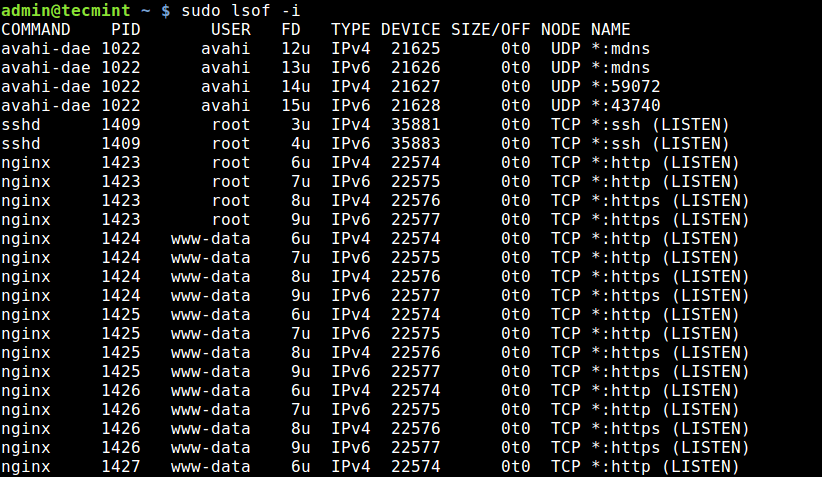
lsof is a powerful command-line utility that provides information about files opened by processes.
In Linux, everything is a file. You can think of a socket as a file that writes to the network.
To get a list of all listening TCP ports with lsof type:
sudo lsof -nP -iTCP -sTCP:LISTENThe options used are as follows:
- -n — Do not convert port numbers to port names.
- -p — Do not resolve hostnames, show numerical addresses.
- -iTCP -sTCP:LISTEN — Show only network files with TCP state LISTEN.
COMMAND PID USER FD TYPE DEVICE SIZE/OFF NODE NAME sshd 445 root 3u IPv4 16434 0t0 TCP *:22 (LISTEN) sshd 445 root 4u IPv6 16445 0t0 TCP *:22 (LISTEN) apache2 515 root 4u IPv6 16590 0t0 TCP *:80 (LISTEN) mysqld 534 mysql 30u IPv6 17636 0t0 TCP *:3306 (LISTEN) mysqld 534 mysql 33u IPv6 19973 0t0 TCP *:33060 (LISTEN) apache2 764 www-data 4u IPv6 16590 0t0 TCP *:80 (LISTEN) apache2 765 www-data 4u IPv6 16590 0t0 TCP *:80 (LISTEN) master 929 root 13u IPv4 19637 0t0 TCP *:25 (LISTEN) master 929 root 14u IPv6 19638 0t0 TCP *:25 (LISTEN) Most of the output columns names are self-explanatory:
- COMMAND , PID , USER — The name, the pid and the user running the program associated with the port.
- NAME — The port number.
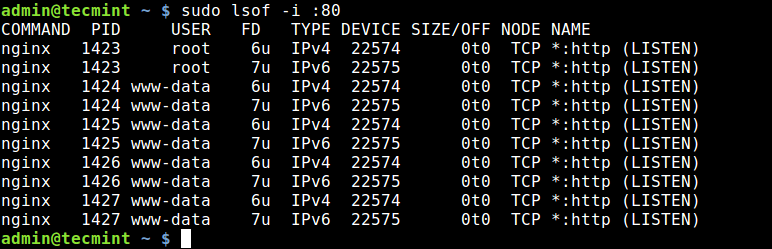
To find what process is listening on a particular port, for example, port 3306 you would use:
sudo lsof -nP -iTCP:3306 -sTCP:LISTENThe output shows that MySQL server uses port 3306 :
COMMAND PID USER FD TYPE DEVICE SIZE/OFF NODE NAME mysqld 534 mysql 30u IPv6 17636 0t0 TCP *:3306 (LISTEN) For more information, visit the lsof man page and read about all other powerful options of this tool.
Conclusion #
We have shown you several commands that you can use to check what ports are in use on your system, and how to find what process listens on a specific port.
If you have any questions or remarks, please leave a comment below.
4 Ways to Find Out What Ports Are Listening in Linux
The state of a port is either open, filtered, closed, or unfiltered. A port is said to be open if an application on the target machine is listening for connections/packets on that port.
In this article, we will explain four ways to check open ports and also will show you how to find which application is listening on what port in Linux.
1. Using Netstat Command
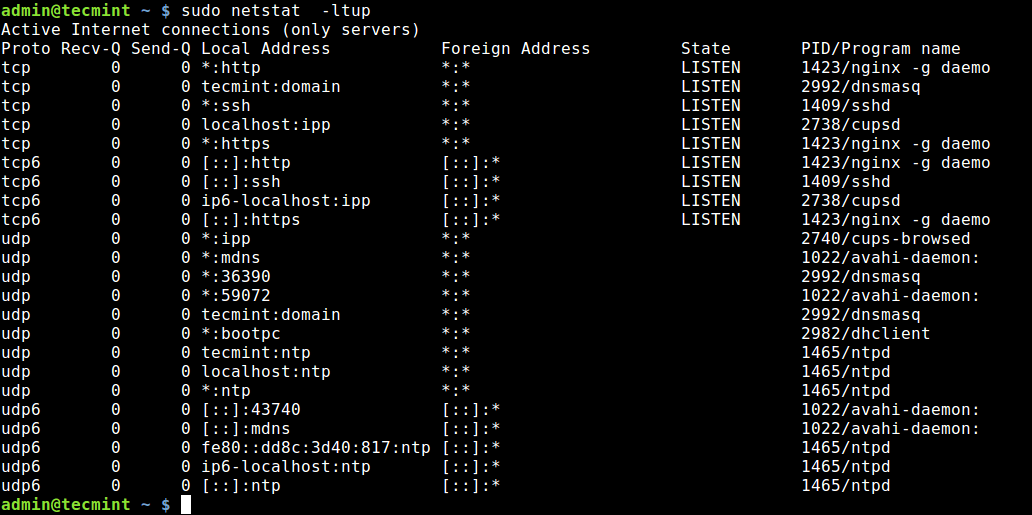
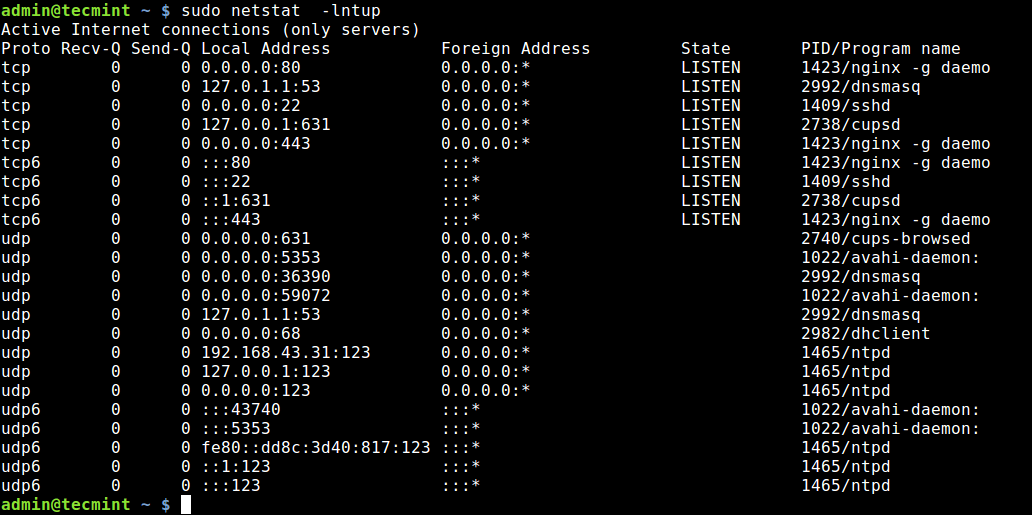
Netstat is a widely used tool for querying information about the Linux networking subsystem. You can use it to print all open ports like this:
The flag -l tells netstat to print all listening sockets, -t shows all TCP connections, -u displays all UDP connections and -p enables printing of application/program name listening on the port.
To print numeric values rather than service names, add the -n flag.
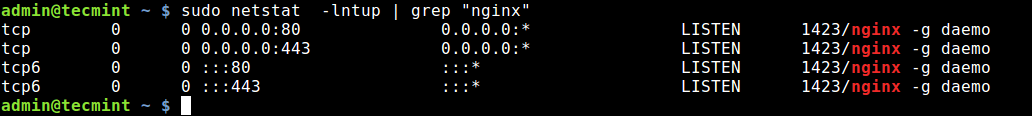
You can also use grep command to find out which application is listening on a particular port, for example.
$ sudo netstat -lntup | grep "nginx"
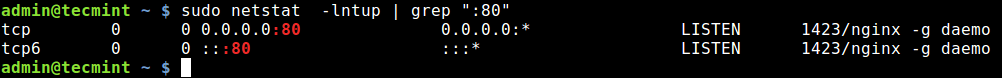
Alternatively, you can specify the port and find the application bound to, as shown.
$ sudo netstat -lntup | grep ":80"
2. Using ss Command
ss command is another useful tool for displaying information about sockets. It’s output looks similar to that of netstat. The following command will show all listening ports for TCP and UDP connections in numeric value.
3. Using Nmap Command
Nmap is a powerful and popular network exploration tool and port scanner. To install nmap on your system, use your default package manager as shown.
$ sudo apt install nmap [On Debian/Ubuntu] $ sudo yum install nmap [On CentOS/RHEL] $ sudo dnf install nmap [On Fedora 22+]
To scan all open/listening ports in your Linux system, run the following command (which should take a long time to complete).
$ sudo nmap -n -PN -sT -sU -p- localhost
4. Using lsof Command
The final tool we will cover for querying open ports is lsof command, which is used to list open files in Linux. Since everything is a file in Unix/Linux, an open file may be a stream or a network file.
To list all Internet and network files, use the -i option. Note that this command shows a mix of service names and numeric ports.
To find which application is listening on a particular port, run lsof in this form.
That’s all! In this article, we have explained four ways to check open ports in Linux. We also showed how to check which processes are bound upon particular ports. You can share your thoughts or ask any questions via the feedback form below.