- How to know what program is listening on a given port?
- 8 Answers 8
- Какой процесс слушает порт в Linux?
- 3 Ways to Find Out Which Process Listening on a Particular Port
- 1. Using netstat Command
- 2. Using lsof Command
- 3. Using fuser Command
- Check Which Process Is Using a Port on Linux
- What Will We Talk About?
- How Are Ports Analogous to Physical Ports?
- A Bit About Port of a Service
- Checking the Ports on Linux
- 1. Lsof Command
- 2. SS Command
- 3. Netstat Command
- 4. Fuser Command
- Conclusion
- About the author
- Ali Imran Nagori
How to know what program is listening on a given port?
I suspect a program is listening on port 8000 on my machine. When I run the following command, I get this error:
> python -m SimpleHTTPServer # Lots of python error socket.error: [Errno 98] Address already in use If I use another port ( 8000 is the default), the web server runs fine. If I run wget localhost:8000 from the command line, it returns 404 Not Found . What can I do (or what tools are available) to find what program is listening on port 8000 , and from there where that program is configured?
8 Answers 8
Open your terminal and type as
that command will list you the application used by that port with PID. (If no results run via sudo since your might have no permission to certain processes.)
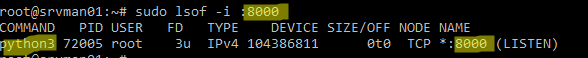
For example, with port 8000 ( python3 -m http.server ):
$ lsof -i :8000 COMMAND PID USER FD TYPE DEVICE SIZE/OFF NODE NAME python3 3269 user 3u IPv4 1783216 0t0 TCP *:8000 (LISTEN) $ sudo lsof -i :22 COMMAND PID USER FD TYPE DEVICE SIZE/OFF NODE NAME sshd 998 root 3u IPv4 1442116 0t0 TCP *:ssh (LISTEN) sshd 998 root 4u IPv6 1442118 0t0 TCP *:ssh (LISTEN) @Imray the example searches for port 8881. The PID column contains the process IDs and the NAME column contains the ports.
You can use netstat to see which process is listening on which port.
You can use this command to have a full detail :
if you need to know exactly which one is listening on port 8000 you can use this :
sudo netstat -peanut | grep ":8000 " There is no process that can hide from netstat.
To kill/end the process use kill
To expound on the answer by @33833 you can get some very detailed info, for example:
$ lsof -i :8000 COMMAND PID USER FD TYPE DEVICE SIZE/OFF NODE NAME squid3 1289 proxy 15u IPv6 14810490 0t0 TCP *:8000 (LISTEN) $ ps -fp 1289 UID PID PPID C STIME TTY TIME CMD proxy 1289 1 0 09:48 ? 00:00:00 /usr/sbin/squid3 -N -f /etc/squid-deb-proxy/squid-deb-proxy.conf I can see right there that squid is the process, but it is actualy my squid-deb-proxy that is taking up the port.
Another good example of a java app:
$ lsof -i :4242 COMMAND PID USER FD TYPE DEVICE SIZE/OFF NODE NAME java 3075 root 86u IPv4 12019 0t0 TCP *:4242 (LISTEN) $ ps -fp 3075 UID PID PPID C STIME TTY TIME CMD root 3075 1 15 May24 ? 3-16:07:25 /usr/local/crashplan/jre/bin/java -Dfile.encoding=UTF-8 -Dapp=CrashPlanService -DappBaseName=CrashPl You can see in lsof (LiSt Open Files) that it is java, which is less than helpful. Running the ps command with the PID we can see right away that it is CrashPlan.
Какой процесс слушает порт в Linux?
17.05.2023
itpro
Linux
Комментариев пока нет
В этой статье мы рассмотрим, как найти процесс, который слушает определенный порт в Linux.
Можно получить информацию о процесс, который слушает определенный порт командой:
В этом примере видно, что порт 8000 занят процессом python3.
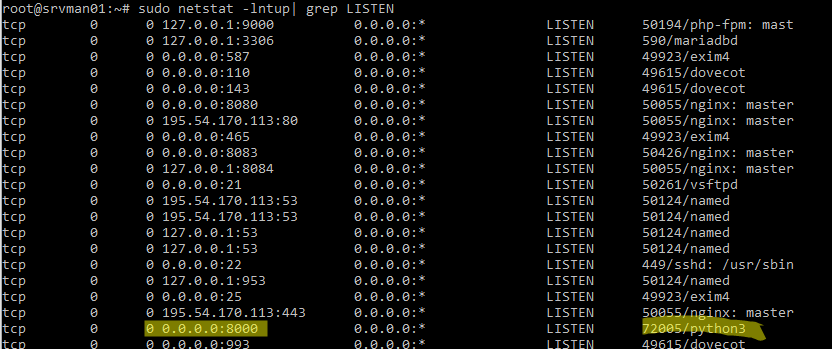
Можно вывести список всех запущенных процессов Linux, который используют любые TCP/UDP порты:
$ sudo netstat -lntup| grep LISTEN
Мы используем следующие ключи:
- -l – показать тольо прослушиваемые порты
- -n – показать IP адреса и номера портов в числовом виде и не пытаться их резолвить (соответствие номеров портов и название служб содержится в файле /etc/services)
- -t – показать открытые TCP порты
- -u – показать UDP порты
- -p – показать название процесс, который прослушивает порт
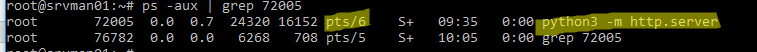
Мы нашли PID процесса ( 72005 ), который использует порт и теперь можно вывести информацию о том, как он запущен:
В этом примере видно, что процесс запущен вручную пользователем root с помощью команды python3 -m http.server (используется для запуска простого HTTP сервера на python для публикации текущего каталога).
Чтобы быстро завершить процесс, который слушает нужный вам порт и освободить его, выполните:
Проверьте, что порт теперь свободен:

Установка и настройка прокси сервера Squid в Linux
Мониторинг срока регистрации (освобождения) домена в Zabbix
Настройка Wi-Fi точки доступа на Linux
Управление конфигурацией Windows через Ansible
3 Ways to Find Out Which Process Listening on a Particular Port
A port is a logical entity that represents an endpoint of communication and is associated with a given process or service in an operating system. In previous articles, we explained how to find out the list of all open ports in Linux and how to check if remote ports are reachable using the Netcat command.
In this short guide, we will show different ways of finding the process/service listening on a particular port in Linux.
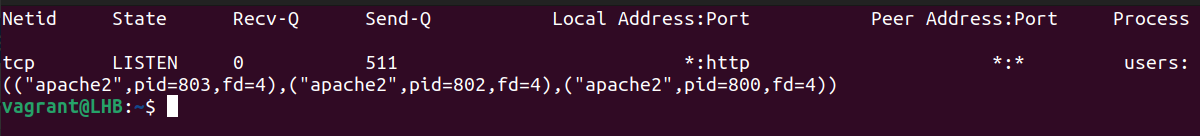
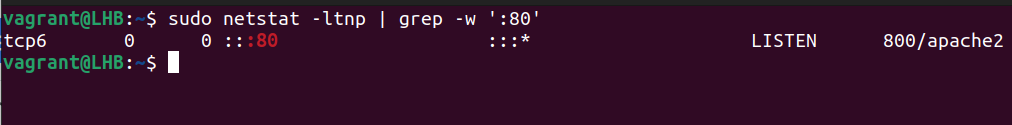
1. Using netstat Command
netstat (network statistics) command is used to display information concerning network connections, routing tables, interface stats, and beyond. It is available on all Unix-like operating systems including Linux and also on Windows OS.
In case you do not have it installed by default, use the following command to install it.
$ sudo apt-get install net-tools [On Debian/Ubuntu & Mint] $ sudo dnf install net-tools [On CentOS/RHEL/Fedora and Rocky Linux/AlmaLinux] $ pacman -S netstat-nat [On Arch Linux] $ emerge sys-apps/net-tools [On Gentoo] $ sudo dnf install net-tools [On Fedora] $ sudo zypper install net-tools [On openSUSE]
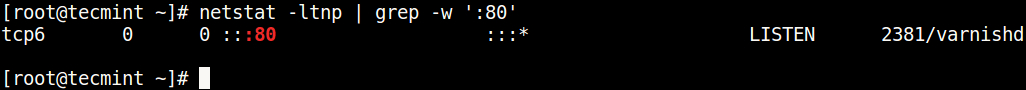
Once installed, you can use it with the grep command to find the process or service listening on a particular port in Linux as follows (specify the port).
In the above command, the flags.
- l – tells netstat to only show listening sockets.
- t – tells it to display tcp connections.
- n – instructs it to show numerical addresses.
- p – enables showing of the process ID and the process name.
- grep -w – shows matching of exact string (:80).
Note: The netstat command is deprecated and replaced by the modern ss command in Linux.
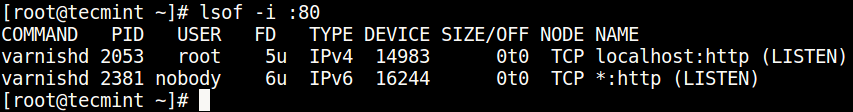
2. Using lsof Command
lsof command (List Open Files) is used to list all open files on a Linux system.
To install it on your system, type the command below.
$ sudo apt-get install lsof [On Debian, Ubuntu and Mint] $ sudo yum install lsof [On RHEL/CentOS/Fedora and Rocky Linux/AlmaLinux] $ sudo emerge -a sys-apps/lsof [On Gentoo Linux] $ sudo pacman -S lsof [On Arch Linux] $ sudo zypper install lsof [On OpenSUSE]
To find the process/service listening on a particular port, type (specify the port).
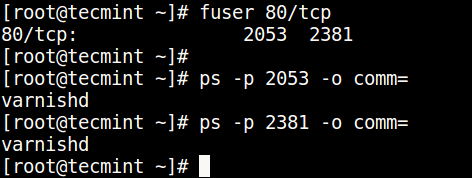
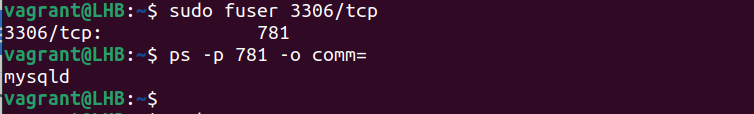
3. Using fuser Command
fuser command shows the PIDs of processes using the specified files or file systems in Linux.
You can install it as follows:
$ sudo apt-get install psmisc [On Debian, Ubuntu and Mint] $ sudo yum install psmisc [On RHEL/CentOS/Fedora and Rocky Linux/AlmaLinux] $ sudo emerge -a sys-apps/psmisc [On Gentoo Linux] $ sudo pacman -S psmisc [On Arch Linux] $ sudo zypper install psmisc [On OpenSUSE]
You can find the process/service listening on a particular port by running the command below (specify the port).
Then find the process name using PID number with the ps command like so.
$ ps -p 2053 -o comm= $ ps -p 2381 -o comm=
You can also check out these useful guides about processes in Linux.
You might also like:
That’s all! Do you know of any other ways of finding the process/service listening on a particular port in Linux, let us know via the comment form below.
Check Which Process Is Using a Port on Linux
In computer networking, a port represents a logical entry and exit point for a connection. Ports are based on software and are entirely virtual. These ports on a computer are managed by the operating system.
What Will We Talk About?
This quick tutorial demonstrates the various methods to determine which Linux process or service is currently listening on a specific port. Let’s talk about ports and their purpose.
How Are Ports Analogous to Physical Ports?
Just as physical ports help to interact with various peripheral devices connected to a computer, ports help the different services to communicate with each other. These services can be on the same computer or on different computers.
A Bit About Port of a Service
To listen for incoming connection requests, a process associates itself with a port number. Most processes are set up with a default port, and they have to use that port as per their specification. They do not automatically switch to the other port unless their configuration is explicitly modified.
A few examples of protocols and their associated default ports include the Secure Shell (SSH) protocol (port22), the Apache HTTP (port80), the MySQL database server (port3306), and so forth. You may use this information to discover which default port does a service utilizes.
The config file of these services can be edited to use some other port as well.
Checking the Ports on Linux
Let’s now see how to check what port/ports a process is using on Linux. Here, we will show you the different commands for this purpose.
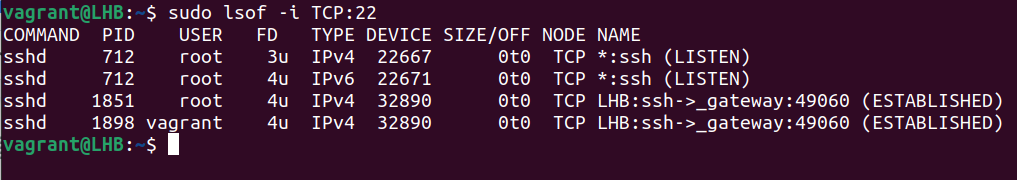
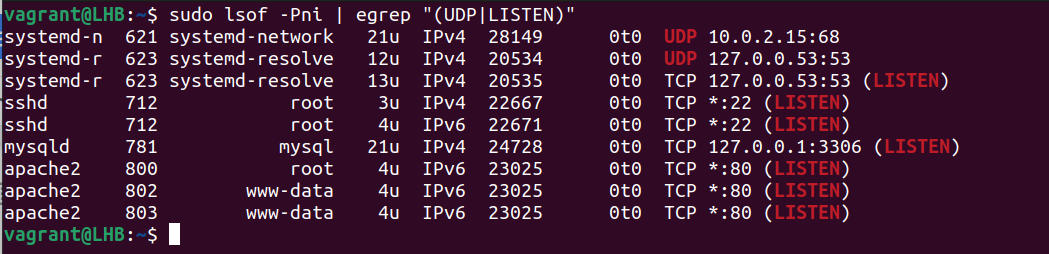
1. Lsof Command
The lsof utility is helpful to obtain a list of the ports which are used by your system. Let’s consider the following example to get an information about a process (processes) using the TCP port 22:
The lsof command gives more information like the user’s name and what process IDs are linked to each process. It works with both TCP and UDP ports.
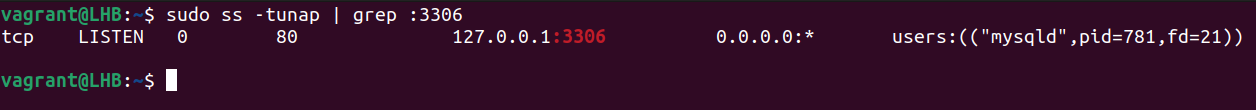
2. SS Command
The ss command is another way to find out which processes are linked to a certain port. Although lsof is the more common abbreviation, some people may find ss to be more handy.
Let’s look for the processes or services that listen on port 3306:
Let’s break down this command:
1. t: It tells the ss command to display the TCP packets.
2. u: It tells the ss command to display the UDP packets.
3. n: It is used to display the port numbers instead of their translations.
4. a: It is used to display the listening as well as non-listening sockets of all types.
5. p: It is used to display the processes that utilize a socket.
The result of the previous command shows which process is utilizing which port. You may also issue the following command:
Here, sport signifies the source port.
These two approaches may help you find the IDs of the processes that are connected to different ports.
3. Netstat Command
The netstat command shows the information about your network and can be used to fix the problems or change the way that your network is set up. It can also keep a close watch on your network connections.
This command is often used to see an information about inbound and outbound connections, routing tables, port listening, and usage stats. Although it has been rendered obsolete in recent years, netstat is still a useful tool for analyzing networks.
With the grep command, netstat can determine which process or service is using a certain port (by mentioning the port):
The options used here can be classified as follows:
1. t: It only shows the TCP connection.
2. l: It is used to display the results in a list.
3. n: It displays addresses and port numbers in numerical format.
4. p: It displays the PID and program name which are associated with each socket.
4. Fuser Command
The fuser command determines the processes that utilize the files or sockets. You can use it to list the services which run on a specific port. Let’s take the example of port 3306 and see what services are running here:
This provides us with the process numbers using this port. You can use this process number to find the corresponding process names. For example, if the process number is 15809, the command to use here is as follows:
However, certain tools are required to identify the processes that utilize a non-standard port. “LSOF” is a tool for discovering what services are available on a network and what ports they use. Consider the following example. This shows how to list the UDP and TCP listening ports:
The following is a description of the options that are used here:
1. P: It suppresses the port service name lookup.
2. n: It displays the numeric network addresses.
3. i: It lists the IP sockets.
Both the ports and the associated processes are shown in the previously-mentioned result. This way is particularly useful for processes with non-default ports.
Conclusion
In this article, we talked about four possible Linux command-line tools and provided the examples on how to use them to find out which process is listening on a certain port.
About the author
Ali Imran Nagori
Ali imran is a technical writer and Linux enthusiast who loves to write about Linux system administration and related technologies. You can connect with him on LinkedIn
.