- How to know what program is listening on a given port?
- 8 Answers 8
- 3 Ways to Find Out Which Process Listening on a Particular Port
- 1. Using netstat Command
- 2. Using lsof Command
- 3. Using fuser Command
- Determine the process pid listening on a certain port
- 8 Answers 8
- Finding the PID of the process using a specific port?
- 7 Answers 7
How to know what program is listening on a given port?
I suspect a program is listening on port 8000 on my machine. When I run the following command, I get this error:
> python -m SimpleHTTPServer # Lots of python error socket.error: [Errno 98] Address already in use If I use another port ( 8000 is the default), the web server runs fine. If I run wget localhost:8000 from the command line, it returns 404 Not Found . What can I do (or what tools are available) to find what program is listening on port 8000 , and from there where that program is configured?
8 Answers 8
Open your terminal and type as
that command will list you the application used by that port with PID. (If no results run via sudo since your might have no permission to certain processes.)
For example, with port 8000 ( python3 -m http.server ):
$ lsof -i :8000 COMMAND PID USER FD TYPE DEVICE SIZE/OFF NODE NAME python3 3269 user 3u IPv4 1783216 0t0 TCP *:8000 (LISTEN) $ sudo lsof -i :22 COMMAND PID USER FD TYPE DEVICE SIZE/OFF NODE NAME sshd 998 root 3u IPv4 1442116 0t0 TCP *:ssh (LISTEN) sshd 998 root 4u IPv6 1442118 0t0 TCP *:ssh (LISTEN) @Imray the example searches for port 8881. The PID column contains the process IDs and the NAME column contains the ports.
You can use netstat to see which process is listening on which port.
You can use this command to have a full detail :
if you need to know exactly which one is listening on port 8000 you can use this :
sudo netstat -peanut | grep ":8000 " There is no process that can hide from netstat.
To kill/end the process use kill
To expound on the answer by @33833 you can get some very detailed info, for example:
$ lsof -i :8000 COMMAND PID USER FD TYPE DEVICE SIZE/OFF NODE NAME squid3 1289 proxy 15u IPv6 14810490 0t0 TCP *:8000 (LISTEN) $ ps -fp 1289 UID PID PPID C STIME TTY TIME CMD proxy 1289 1 0 09:48 ? 00:00:00 /usr/sbin/squid3 -N -f /etc/squid-deb-proxy/squid-deb-proxy.conf I can see right there that squid is the process, but it is actualy my squid-deb-proxy that is taking up the port.
Another good example of a java app:
$ lsof -i :4242 COMMAND PID USER FD TYPE DEVICE SIZE/OFF NODE NAME java 3075 root 86u IPv4 12019 0t0 TCP *:4242 (LISTEN) $ ps -fp 3075 UID PID PPID C STIME TTY TIME CMD root 3075 1 15 May24 ? 3-16:07:25 /usr/local/crashplan/jre/bin/java -Dfile.encoding=UTF-8 -Dapp=CrashPlanService -DappBaseName=CrashPl You can see in lsof (LiSt Open Files) that it is java, which is less than helpful. Running the ps command with the PID we can see right away that it is CrashPlan.
3 Ways to Find Out Which Process Listening on a Particular Port
A port is a logical entity that represents an endpoint of communication and is associated with a given process or service in an operating system. In previous articles, we explained how to find out the list of all open ports in Linux and how to check if remote ports are reachable using the Netcat command.
In this short guide, we will show different ways of finding the process/service listening on a particular port in Linux.
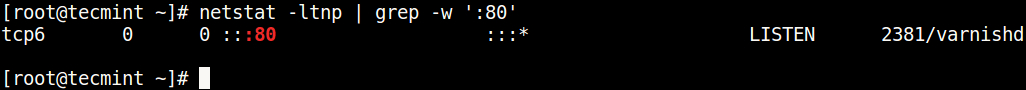
1. Using netstat Command
netstat (network statistics) command is used to display information concerning network connections, routing tables, interface stats, and beyond. It is available on all Unix-like operating systems including Linux and also on Windows OS.
In case you do not have it installed by default, use the following command to install it.
$ sudo apt-get install net-tools [On Debian/Ubuntu & Mint] $ sudo dnf install net-tools [On CentOS/RHEL/Fedora and Rocky Linux/AlmaLinux] $ pacman -S netstat-nat [On Arch Linux] $ emerge sys-apps/net-tools [On Gentoo] $ sudo dnf install net-tools [On Fedora] $ sudo zypper install net-tools [On openSUSE]
Once installed, you can use it with the grep command to find the process or service listening on a particular port in Linux as follows (specify the port).
In the above command, the flags.
- l – tells netstat to only show listening sockets.
- t – tells it to display tcp connections.
- n – instructs it to show numerical addresses.
- p – enables showing of the process ID and the process name.
- grep -w – shows matching of exact string (:80).
Note: The netstat command is deprecated and replaced by the modern ss command in Linux.
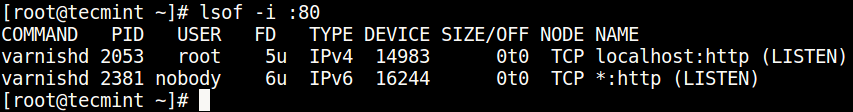
2. Using lsof Command
lsof command (List Open Files) is used to list all open files on a Linux system.
To install it on your system, type the command below.
$ sudo apt-get install lsof [On Debian, Ubuntu and Mint] $ sudo yum install lsof [On RHEL/CentOS/Fedora and Rocky Linux/AlmaLinux] $ sudo emerge -a sys-apps/lsof [On Gentoo Linux] $ sudo pacman -S lsof [On Arch Linux] $ sudo zypper install lsof [On OpenSUSE]
To find the process/service listening on a particular port, type (specify the port).
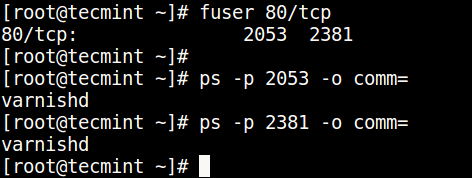
3. Using fuser Command
fuser command shows the PIDs of processes using the specified files or file systems in Linux.
You can install it as follows:
$ sudo apt-get install psmisc [On Debian, Ubuntu and Mint] $ sudo yum install psmisc [On RHEL/CentOS/Fedora and Rocky Linux/AlmaLinux] $ sudo emerge -a sys-apps/psmisc [On Gentoo Linux] $ sudo pacman -S psmisc [On Arch Linux] $ sudo zypper install psmisc [On OpenSUSE]
You can find the process/service listening on a particular port by running the command below (specify the port).
Then find the process name using PID number with the ps command like so.
$ ps -p 2053 -o comm= $ ps -p 2381 -o comm=
You can also check out these useful guides about processes in Linux.
You might also like:
That’s all! Do you know of any other ways of finding the process/service listening on a particular port in Linux, let us know via the comment form below.
Determine the process pid listening on a certain port
As the title says, I’m running multiple game servers, and every of them has the same name but different PID and the port number. I would like to match the PID of the server which is listening on certain port, and then I would like to kill this process. I need that in order to complete my bash script. Is that even possible? Because it didn’t find yet any solutions on the web.
8 Answers 8
Short version which you can pass to kill command:
This also includes processes that are connected on that port. lsof -i4TCP:80 -sTCP:LISTEN -t is probably what you want, instead.
Exactly what I was looking for. I wanted to kill a process by searching for the port it is running at.
@Nevir what do you mean by » also includes processes that are connected on that port»? Can you please explain?
The -p flag of netstat gives you PID of the process:
*use sudo if showing — instead of PID
Edit: The command that is needed to get PIDs of socket users in FreeBSD is sockstat . As we worked out during the discussion with @Cyclone, the line that does the job is:
sockstat -4 -l | grep :80 | awk '' | head -1 netstat: 80: unknown or uninstrumented protocol used the 80 (nginx) port for testing purpoes. Not worked.
netstat -p -l | grep $PORT and lsof -i :$PORT solutions are good but I prefer fuser $PORT/tcp extension syntax to POSIX (which work for coreutils ) as with pipe:
it prints pure pid so you can drop sed magic out.
One thing that makes fuser my lover tools is ability to send signal to that process directly (this syntax is also extension to POSIX):
$ fuser -k $port/tcp # with SIGKILL $ fuser -k -15 $port/tcp # with SIGTERM $ fuser -k -TERM $port/tcp # with SIGTERM Finding the PID of the process using a specific port?
I am installing hadoop on my Ubuntu system. When I start it, it reports that port 9000 is busy. I used:
tcp 0 0 127.0.0.1:9000 0.0.0.0:* LISTEN netstat command might work in many operations systems to allow you get that, you just have to find the arguments that will ensure it will show pids along each known opened port.
7 Answers 7
Your existing command doesn’t work because Linux requires you to either be root or the owner of the process to get the information you desire.
On modern systems, ss is the appropriate tool to use to get this information:
$ sudo ss -lptn 'sport = :80' State Local Address:Port Peer Address:Port LISTEN 127.0.0.1:80 *:* users:(("nginx",pid=125004,fd=12)) LISTEN ::1:80 . * users:(("nginx",pid=125004,fd=11)) You can also use the same invocation you’re currently using, but you must first elevate with sudo :
$ sudo netstat -nlp | grep :80 tcp 0 0 0.0.0.0:80 0.0.0.0:* LISTEN 125004/nginx $ sudo lsof -n -i :80 | grep LISTEN nginx 125004 nginx 3u IPv4 6645 0t0 TCP 0.0.0.0:80 (LISTEN) @AdamB Unless a Mac user arrived here searching for Finding the PID of the process using a specific port
Also you can use lsof utility. Need to be root.
# lsof -i :25 COMMAND PID USER FD TYPE DEVICE SIZE/OFF NODE NAME exim4 2799 Debian-exim 3u IPv4 6645 0t0 TCP localhost:smtp (LISTEN) exim4 2799 Debian-exim 4u IPv6 6646 0t0 TCP localhost:smtp (LISTEN) This command will also give you processes with established connections, not just processes that are listening .
Not necessarily to be root. And, for those who want to get PID only, you can lsof -i :25 -Fp , which produces output like p1234 .
Important to note that you may need to run as sudo as some processes may be inaccessible to the user.
I am using «CentOS 7 minimal» which has nor netstat neither lsof . But a lot of linux distributions have the socket statistics command (i.e. ss ).
Here is an example of execution:
# ss -tanp | grep 6379 LISTEN 0 128 127.0.0.1:6379 *:* users:(("redis-server",pid=2531,fd=4)) USER PID ACCESS COMMAND 22/tcp: root 598 F. sshd This is a good thing to remember generally. Commands in Linux generally won’t give information on processes started by root/sudo unless the command is run with Sudo. This is true even when the command does not normally need sudo to run correctly.
Running the command with sudo would give you the PID . On my development machine I get:
$ netstat -nlp | grep 8080 tcp6 0 0 . 8080 . * LISTEN - $ sudo netstat -nlp | grep 8080 tcp6 0 0 . 8080 . * LISTEN 16449/java And as mentioned in other answers you can also use the ss or the lsof commands.
I’m working on a Yocto Linux system that has a limited set of available Linux tools. I managed to find the process of a running port using the following commands (where I find the process using port 1883):
root@root:~# netstat -lt Active Internet connections (only servers) Proto Recv-Q Send-Q Local Address Foreign Address State tcp 0 0 0.0.0.0:hostmon 0.0.0.0:* LISTEN tcp 0 0 localhost.localdomain:domain 0.0.0.0:* LISTEN tcp 0 0 0.0.0.0:9080 0.0.0.0:* LISTEN tcp 0 0 0.0.0.0:1883 0.0.0.0:* LISTEN tcp 0 0 . hostmon . * LISTEN tcp 0 0 localhost:domain . * LISTEN tcp 0 0 . ssh . * LISTEN tcp 0 0 . 1883 . * LISTEN root@root:~# fuser 1883/tcp 290 root@root:~# ps | grep 290 290 mosquitt 25508 S /usr/sbin/mosquitto -c /etc/mosquitto/mosquitto.conf 12141 root 8444 S grep 290 As we can see above, it’s the program /usr/sbin/mosquitto that’s using port 1883.
Proto Recv-Q Send-Q Local Address Foreign Address State Benutzer Inode PID/Program name tcp 0 0 127.0.0.1:25 0.0.0.0:* LISTEN 0 55233 - tcp 0 0 0.0.0.0:8080 0.0.0.0:* LISTEN 1000 3166326 364815/node tcp 0 0 127.0.0.1:33060 0.0.0.0:* LISTEN 127 36032 - tcp 0 0 127.0.0.1:587 0.0.0.0:* LISTEN 0 55234 - tcp 0 0 127.0.0.1:631 0.0.0.0:* LISTEN 0 2927660 - tcp 0 0 127.0.0.1:3306 0.0.0.0:* LISTEN 127 36034 - tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN 0 30995 - tcp 0 0 127.0.0.53:53 0.0.0.0:* LISTEN 101 26903 - tcp 0 0 127.0.0.1:6379 0.0.0.0:* LISTEN 132 32262 - tcp6 0 0 127.0.0.1:9300 . * LISTEN 129 40952 - tcp6 0 0 . 35729 . * LISTEN 1000 3088940 355480/grunt tcp6 0 0 ::1:9300 . * LISTEN 129 40945 - tcp6 0 0 ::1:9200 . * LISTEN 129 41261 - tcp6 0 0 ::1:631 . * LISTEN 0 2927659 - tcp6 0 0 127.0.0.1:9200 . * LISTEN 129 41262 - tcp6 0 0 . 9003 . * LISTEN 1000 3234646 373445/code tcp6 0 0 . 22 . * LISTEN 0 31006 - tcp6 0 0 . 80 . * LISTEN 0 940224 - tcp6 0 0 ::1:6379 . * LISTEN 132 32263 - udp 0 0 127.0.0.53:53 0.0.0.0:* 101 26902 - udp 0 0 0.0.0.0:631 0.0.0.0:* 0 2927684 - udp 0 0 0.0.0.0:5353 0.0.0.0:* 115 29345 - udp 0 0 0.0.0.0:42443 0.0.0.0:* 115 29347 - udp6 0 0 . 5353 . * 115 29346 - udp6 0 0 . 34477 . * 115 29348 -