- Everything Important You Need to Know About UID in Linux
- What is UID in Linux?
- How to find the UID of a user in Linux?
- How to change UID of a user in Linux?
- How does UID associate with different system resources? [for advanced users]
- UID and files
- UID and processes
- Linux File Permission: uid vs gid
- What are Uid and Gid?
- How to Create and Mount a Linux File System
- How to Display a Uid and Gid
- Final Thoughts: What’s Next?
Everything Important You Need to Know About UID in Linux
This Linux Basics guide teaches you everything important associated with UID in Linux.
What is UID in Linux?
UID stands for user identifier. A UID is a number assigned to each Linux user. It is the user’s representation in the Linux kernel. The UID is used for identifying the user within the system and for determining which system resources the user can access. This is why the user ID should be unique.
You can find UID stored in the /etc/passwd file. This is the same file that can be used to list all the users in a Linux system.
Use a Linux command to view text file and you’ll see various information about the users present on your system.
root:x:0:0:root:/root:/bin/bash daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin bin:x:2:2:bin:/bin:/usr/sbin/nologin sys:x:3:3:sys:/dev:/usr/sbin/nologin sync:x:4:65534:sync:/bin:/bin/sync games:x:5:60:games:/usr/games:/usr/sbin/nologin man:x:6:12:man:/var/cache/man:/usr/sbin/nologin lp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologin mail:x:8:8:mail:/var/mail:/usr/sbin/nologin news:x:9:9:news:/var/spool/news:/usr/sbin/nologin johndoe:x:1000:1000:John Doe. /home/helder:/bin/bash davmail:x:127:65534::/var/lib/davmail:/usr/sbin/nologin statd:x:128:65534::/var/lib/nfs:/usr/sbin/nologinThe third field here represents the user ID or UID.
Do note that in most Linux distributions, UID 1-500 are usually reserved for system users. In Ubuntu and Fedora, UID for new users start from 1000.
For example, if you use adduser or useradd command to create a new user, it will get the next available number after 1000 as its UID.
How to find the UID of a user in Linux?
You can always rely on the /etc/passwd file to get the UID of a user. That’s not the only way to get the UID information in Linux.
The id command in Linux will display the UID, GID and groups your current user belongs to:
id uid=1000(abhishek) gid=1000(abhishek) groups=1000(abhishek),4(adm),24(cdrom),27(sudo),30(dip),46(plugdev),116(lpadmin),126(sambashare),127(kvm)You can also specify the user names with the id command to get the UID of any Linux user:
id standard uid=1001(standard) gid=1001(standard) groups=1001(standard)How to change UID of a user in Linux?
Suppose you had several users on your Linux system. You had to delete a user because he/she left the organization. Now you want its UID to be taken by another user already on the system.
You can change the UID by modifying the user using usermod command like this:
You need to have superuser privilege to execute the above command.
Do you remember the file permission and ownership concept in Linux? The ownership of a file is determined by the UID of the owner user.
When you update the UID of a user, what happens to the files owned by this user?While all the files in the home directory of user_2 will have their associated UID changed, you’ll have to manually update the associated UID of other files outside the home directory.
What you can do is manually update the ownership of the files associated with the old UID of the user_2.
find / -user old_uid_of_user_2 -exec chown -h user_2 <> \;How does UID associate with different system resources? [for advanced users]
UIDs are unique to one another and thus they can also be used to identify ownership of different system resources such as files and processes.
UID and files
I hope you are familiar with the file permission concept in Linux. When you’re creating a file, you’re the owner of this file. Now you can decide who gets to do what with this file. This is part of Linux’s DAC mechanism where each file is left at its owner’s discretion.
You can read a file’s ownership by using either ls or stat command. Let’s do it with the popular ls command and check the ownership of either the binary sleep or passwd .
As you can see, the file /usr/bin/sleep belongs to root:
ls -l $(which sleep) -rwxr-xr-x 1 root root 39048 Mar 6 2020 /usr/bin/sleepLet’s force it to map the ownership with UID instead of username:
ls -lhn $(which sleep) -rwxr-xr-x 1 0 0 39K Mar 6 2020 /usr/bin/sleepHere’s fun information. Your operating system doesn’t understand «usernames». Whenever a program needs to work with usernames or needs to print such, it refers to the /etc/passwd file to extract the information.
You don’t have to take my words for it. See it yourself with strace program which prints all the system calls made by a program.
strace ls -lhn $(which sleep) 2>&1 | grep passwd What you are trying to see is whether ls command is trying to read the /etc/passwd file or not.
strace ls -lh $(which sleep) 2>&1 | grep passwd openat(AT_FDCWD, "/etc/passwd", O_RDONLY|O_CLOEXEC) = 6UID and processes
Processes have owners too, just like files. Only the owner (or the root user) of a process can send process signals to it. This is where the UID comes into play.
If a normal user tries to kill a process owned by another user, it will result in error:
kill 3708 bash: kill: (3708) - Operation not permittedOnly the owner of the process or the root can do this.
A process must be regulated. Regulated as in you need to have a way to limit or know how much a process is allowed to do. This is determined by its UID(s).
There are three types of UIDs associated with a process.
- Real UID: Real UID is the UID that a process adopts from its parent. In easier terms, whoever starts a process, the UID of that user is the real UID of the process. This is helpful in identifying who a process really belongs to. This is essential especially when the effective UID is not the same as the real UID which I’m going to talk about next.
- Effective UID: This is what mostly determines what permissions a certain process really has. While a user can start the process, it can run with a different user’s available permissions. The command passwd is one example of this. This program edits the file /etc/shadow , which is root owned. Therefore, a normal user shouldn’t be able to run this command or change his/her password. Luckily, the binary runs with an effective UID of 0 (i.e. root), which enables it to have enough privilege to edit the /etc/shadow file. Real and effective UIDs are mostly the same except in the case of SUID bit enabled binaries.
- Saved UID: UID that’s available at a process’s disposal. This one is not normally used, but is still there in case the process knows it’s not going to perform any privileged work, so it can change its effective UID to something that’s unprivileged. This reduces the surface of an unintentional misbehavior.
That’s it. I hope you have a better idea about UID in Linux now. Don’t hesitate to ask your questions, if any.
As a pro Linux user, if you think I missed some important concept about UID, please let me know in the comment section.
Linux File Permission: uid vs gid
The uid (user identifier) and gid (group identifier) are important fundamental concepts for Linux system administration. With that being said, it is critical to understand them before achieving a Linux certification. Understanding how uid and gid affect file permissions and how programs run can make you a better exam taker, administrator, or security pro.
Here, we’ll take a quick look at what the uid and gid are, how to display them, and how they can help you better understand Linux file permissions.
What are Uid and Gid?
As you might expect, uid is a number associated with a user account and gid is a number associated with a group.
How to Create and Mount a Linux File System
The root user and group are usually given uid and gid 0. The IDs from 1-99 are also reserved for use by other system accounts. What happens after ID 99 tends to vary by operating system. For example, some flavors of *nix reserve 100-499 for dynamic system allocation (e.g. if a package you install needs a uid/gid) and begin allocating standard user accounts uid and gid numbers at 500. Other systems, reserve 100-999 for dynamic system allocation and start standard user accounts from 1,000 and up.
Uid and gid matter for more than just identifying users and groups. When a process is started or a command is run, the uid or gid that called it dictates privileges and file system access. For example, uid and gid values help your Linux systems differentiate between root and a user with lower privileges.
How to Display a Uid and Gid
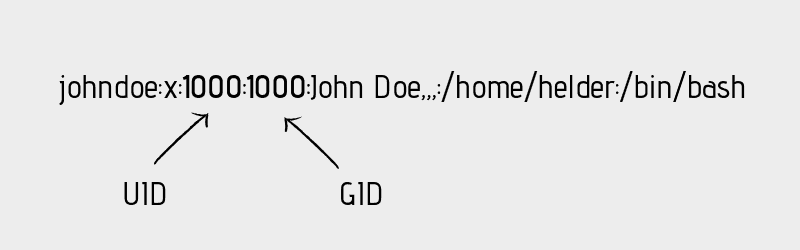
There are a few ways to view a uid and gid. One of the simplest is looking at the /etc/passwd file available on most Linux operating systems. In the /etc/passwd file the uid is the 3rd field and the gid is the 4th.
For example, on our Ubuntu 20.04 system where «cooluser» was the first account created, we can see that cooluser’s uid and gid are 1000.
cooluser@LAPTOP-5V55HON5:~$ cat /etc/passwd | grep cooluser cooluser:x:1000:1000. /home/cooluser:/bin/bash cooluser@LAPTOP-5V55HON5:~$You can also check the gid and uid of your current user or other users with the aptly named id command. In the examples below, we use id to check our own uid and gid as well as the uid and gid of «otheruser» with the command id otheruser.
cooluser@LAPTOP-5V55HON5:~$ id uid=1000(cooluser) gid=1000(cooluser) groups=1000(cooluser),4(adm),20(dialout),24(cdrom),25(floppy),27(sudo),29(audio),30(dip),44(video),46(plugdev),117(netdev) cooluser@LAPTOP-5V55HON5:~$ id otheruser uid=1001(otheruser) gid=1001(otheruser) groups=1001(otheruser) cooluser@LAPTOP-5V55HON5:~$You’ll notice that there are multiple groups in id cooluser command. This is because the id command prints the real uid/gid, the effective uid/gid usually the same as the real uid/gid, but not always, and supplementary group IDs. These values come into play once you dive into file permissions and concepts like setuid.
Final Thoughts: What’s Next?
We hope this crash course was helpful! Understanding gid and uid is important foundational knowledge for Linux professionals. From here, you dive further into Linux file system permissions or user administration. If you’re still not sure where to start but know you want to improve your *nix skills, check out Shawn Powers’ Linux Essentials training. Whichever path you take, the important thing is to keep stacking your skills.