- How to spoof the MAC address of a network interface on Linux
- Why Spoof a MAC Address?
- How to Spoof a MAC Address Temporarily
- Method One: iproute2
- Method Two: macchanger
- To spoof a MAC address to a different value:
- To spoof a MAC address to a random value while preserving the same OUI:
- To spoof a MAC address to a completely random value:
- To get all MAC address OUIs associated with a particular vendor (e.g., Juniper):
- To show the original permanent and spoofed MAC addresses:
- How to Spoof a MAC Address Permanently
- On CentOS/RHEL or Fedora without Network Manager:
- On CentOS/RHEL, Fedora, Debian/Ubuntu with Network Manager:
- On Debian/Ubuntu without Network Manager:
- Support Xmodulo
- MAC address spoofing
- Manually
- iproute2
- macchanger
- Automatically
- systemd-udevd
- systemd.link
- udev rule
- systemd unit
- Creating unit
- Enabling service
- netctl interfaces
- NetworkManager
- wpa_supplicant
- iwd
- Troubleshooting
- Connection to DHCPv4 network fails
- See also
How to spoof the MAC address of a network interface on Linux
A 48-bit MAC address (e.g., 08:4f:b5:05:56:a0) is a globally unique identifier associated with a physical network interface, which is assigned by a manufacturer of the corresponding network interface card. Higher 24 bits in a MAC address (also known as OUI or «Organizationally Unique Identifier») uniquely identify the organization which has issued the MAC address, so that there is no conflict among all existing MAC addresses.
While a MAC address is a manufacturer-assigned hardware address, it can actually be modified by a user. This practice is often called MAC address spoofing. In this tutorial, I am going to show how to spoof the MAC address of a network interface on Linux.
Why Spoof a MAC Address?
There could be several technical reasons you may want to change a MAC address. Some ISPs authenticate a subscriber’s Internet connection via the MAC address of their home router. Suppose your router is just broken in such a scenario. While your ISP re-establishes your Internet access with a new router, you could temporarily restore the Internet access by changing the MAC address of your computer to that of the broken router.
Many DHCP servers lease IP addresses based on MAC addresses. Suppose for any reason you need to get a different IP address via DHCP than the current one you have. Then you could spoof your MAC address to get a new IP address via DHCP, instead of waiting for the current DHCP lease to expire who knows when.
Technical reasons aside, there are also legitimate privacy and security reasons why you wish to hide your real MAC address. Unlike your layer-3 IP address which can change depending on the networks you are connected to, your MAC address can uniquely identify you wherever you go. Call me a paranoid, but you know what this means to your privacy. There is also a well-known exploit called piggybacking, where a hacker snoops on your MAC address on a public WiFi network, and attempts to impersonate you using your MAC address while you are away.
How to Spoof a MAC Address Temporarily
On Linux, you can switch MAC addresses temporarily at run time. In this case, the changed MAC address will revert to the original when you reboot. Note that you will lose your network connection momentarily during MAC address transition. On Linux, there are several easy ways to change a MAC address at run time.
Method One: iproute2
$ sudo ip link set dev eth0 down $ sudo ip link set dev eth0 address 00:00:00:00:00:01 $ sudo ip link set dev eth0 up
Method Two: macchanger
A command-line utility called macchanger allows you to change MAC addresses from known vendor list.
To install macchanger on Ubuntu, Debian or Linux Mint:
$ sudo apt-get install macchanger
To install macchanger on Fedora:
$ sudo yum install macchangerTo install
macchanger on CentOS or RHEL: $ wget http://ftp.club.cc.cmu.edu/pub/gnu/macchanger/macchanger-1.6.0.tar.gz $ tar xvfvz macchanger-1.6.0.tar.gz $ cd macchanger-1.6.0 $ ./configure $ make $ sudo make install
The following examples are some of advanced usages of macchanger . With macchanger , you no longer have to deactivate/reactivate a network interface manually.
To spoof a MAC address to a different value:
$ sudo macchanger --mac=00:00:00:00:00:01 eth0
To spoof a MAC address to a random value while preserving the same OUI:
To spoof a MAC address to a completely random value:
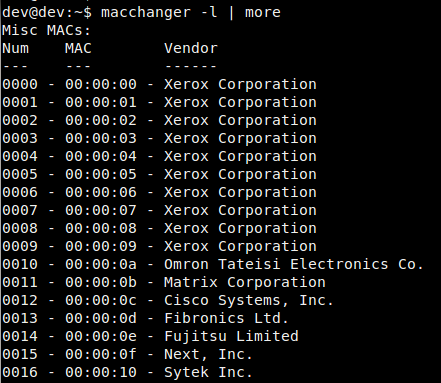
To get all MAC address OUIs associated with a particular vendor (e.g., Juniper):
$ macchanger -l | grep -i juniper
To show the original permanent and spoofed MAC addresses:
Current MAC: 56:95:ac:ee:6e:77 (unknown) Permanent MAC: 00:0c:29:97:68:02 (Vmware, Inc.)
How to Spoof a MAC Address Permanently
If you want to spoof your MAC address permanently across reboots, you can specify the spoofed MAC address in interface configuration files. For example, if you want to change the MAC address of eth0 , do the following.
On CentOS/RHEL or Fedora without Network Manager:
$ sudo vi /etc/sysconfig/network-scripts/ifcfg-eth0
DEVICE=eth0 MACADDR=00:00:00:00:00:01
On CentOS/RHEL, Fedora, Debian/Ubuntu with Network Manager:
On these systems, you can create a custom startup script in /etc/NetworkManager/dispatcher.d as follows. I assume that you already installed macchanger .
$ sudo vi /etc/NetworkManager/dispatcher.d/000-changemac
#!/bin/bash case "$2" in up) macchanger --mac=00:00:00:00:00:01 "$1" ;; esac
$ sudo chmod 755 /etc/NetworkManager/dispatcher.d/000-changemac
On Debian/Ubuntu without Network Manager:
Create a custom startup script in /etc/network/if-up.d/ as follows.
$ sudo vi /etc/network/if-up.d/changemac
#!/bin/sh if [ "$IFACE" = eth0 ]; then ip link set dev "$IFACE" address 00:00:00:00:00:01 fi
$ sudo chmod 755 /etc/network/if-up.d/changemac
Support Xmodulo
This website is made possible by minimal ads and your gracious donation via PayPal or credit card
Please note that this article is published by Xmodulo.com under a Creative Commons Attribution-ShareAlike 3.0 Unported License. If you would like to use the whole or any part of this article, you need to cite this web page at Xmodulo.com as the original source.
MAC address spoofing
This article gives several methods to spoof a Media Access Control (MAC) address.
Manually
There are two methods for spoofing a MAC address: installing and configuring either iproute2 or macchanger . Both of them are outlined below.
iproute2
First, you can check your current MAC address with the command:
# ip link show interface
where interface is the name of your network interface.
The section that interests us at the moment is the one that has «link/ether» followed by a 6-byte number. It will probably look something like this:
The first step to spoofing the MAC address is to bring the network interface down. It can be accomplished with the command:
# ip link set dev interface down
Next, we actually spoof our MAC. Any hexadecimal value will do, but some networks may be configured to refuse to assign IP addresses to a client whose MAC does not match up with any of known vendors. Therefore, unless you control the network(s) you are connecting to, use MAC prefix of any real vendor (basically, the first three bytes), and use random values for next three bytes. For more information please read Wikipedia:Organizationally unique identifier.
To change the MAC, we need to run the command:
# ip link set dev interface address XX:XX:XX:XX:XX:XX
Where any 6-byte value will suffice for XX:XX:XX:XX:XX:XX .
The final step is to bring the network interface back up. This can be accomplished by running the command:
# ip link set dev interface up
If you want to verify that your MAC has been spoofed, simply run ip link show interface again and check the value for ‘link/ether’. If it worked, ‘link/ether’ should be whatever address you decided to change it to.
macchanger
Another method uses macchanger (a.k.a., the GNU MAC Changer). It provides a variety of features such as changing the address to match a certain vendor or completely randomizing it.
The spoofing is done on per-interface basis, specify network interface name as interface in each of the following commands.
The MAC address can be spoofed with a fully random address:
# macchanger -r interface
To randomize only device-specific bytes of current MAC address (that is, so that if the MAC address was checked it would still register as being from the same vendor), you would run the command:
# macchanger -e interface
To change the MAC address to a specific value, you would run:
# macchanger --mac=XX:XX:XX:XX:XX:XX interface
Where XX:XX:XX:XX:XX:XX is the MAC you wish to change to.
Finally, to return the MAC address to its original, permanent hardware value:
# macchanger -p interface
Note: A device cannot be in use (connected in any way or with its interface up) while the MAC address is being changed.
Automatically
systemd-udevd
udev allows you to perform MAC address spoofing by creating systemd.link(5) files or udev rules.
systemd.link
To set a static spoofed MAC address:
/etc/systemd/network/01-mac.link
[Match] PermanentMACAddress=original MAC [Link] MACAddress=spoofed MAC
To randomize the MAC address on every boot, set MACAddressPolicy=random instead of MACAddress=spoofed MAC .
udev rule
Use address attribute to match the correct device by its original MAC address and change it using the ip command:
/etc/udev/rules.d/81-mac-spoof.rules
ACTION=="add", SUBSYSTEM=="net", ATTR= , RUN+
systemd unit
Creating unit
Below you find two examples of systemd units to change a MAC address at boot, one sets a static MAC using ip and one uses macchanger to assign a random MAC address. The systemd network-pre.target is used to ensure the MAC is changed before a network manager like Netctl or NetworkManager, systemd-networkd or dhcpcd service starts.
iproute2
systemd unit setting a predefined MAC address:
/etc/systemd/system/macspoof@.service
[Unit] Description=MAC Address Change %I Wants=network-pre.target Before=network-pre.target BindsTo=sys-subsystem-net-devices-%i.device After=sys-subsystem-net-devices-%i.device [Service] Type=oneshot ExecStart=/usr/bin/ip link set dev %i address 36:aa:88:c8:75:3a ExecStart=/usr/bin/ip link set dev %i up [Install] WantedBy=multi-user.target
macchanger
systemd unit setting a random address while preserving the original NIC vendor bytes. Ensure that macchanger is installed:
/etc/systemd/system/macspoof@.service
[Unit] Description=macchanger on %I Wants=network-pre.target Before=network-pre.target BindsTo=sys-subsystem-net-devices-%i.device After=sys-subsystem-net-devices-%i.device [Service] ExecStart=/usr/bin/macchanger -e %I Type=oneshot [Install] WantedBy=multi-user.target
A full random address can be set using the -r option, see #macchanger.
Enabling service
Append the desired network interface to the service name (e.g. eth0 ) and enable the service (e.g. macspoof@eth0.service ).
Reboot, or stop and start the prerequisite and requisite services in the proper order. If you are in control of your network, verify that the spoofed MAC has been picked up by your router by examining the static, or DHCP address tables within the router.
netctl interfaces
You can use a netctl hook to run a command each time a netctl profile is re-/started for a specific network interface. Replace interface accordingly:
/etc/netctl/interfaces/interface
#!/usr/bin/env sh /usr/bin/macchanger -r interface
NetworkManager
wpa_supplicant
wpa_supplicant can use random MAC address for each ESS connection(AP) (see [1] for details).
Add this to your configuration:
/etc/wpa_supplicant/wpa_supplicant-wlan0.conf
mac_addr=1 preassoc_mac_addr=1 gas_rand_mac_addr=1
iwd
To randomize the MAC address when iwd starts (see iwd.config(5) for details):
[General] AddressRandomization=once AddressRandomizationRange=nic
Specifying AddressRandomizationRange enables control over which part of the address is randomized. If set to nic , only the NIC specific octets (last three octets) are randomized. The permanent mac address of the network interface is used for the initial 3 octets. If set to full , all six octets of the address are randomized.
Troubleshooting
Connection to DHCPv4 network fails
If you cannot connect to a DHCPv4 network and you are using dhcpcd, which is the default for NetworkManager, you might need to modify the dhcpcd configuration to obtain a lease.