- How to Manage Users and Groups in Linux
- Manage Users and Groups in Linux
- What is a Linux user?
- Linux System users
- Linux Regular users
- Linux user Accounts:
- Assign Password to a Linux user
- Delete Linux user
- Modifying users properties in Linux
- Update the comment part
- Change User Home Directory
- Setting User Account Expiry Date
- Lock and unlock the user account
- Group Management
- Create a Linux Group
- Add users to a Linux group
- Change name of a Linux group
- Change GID of a Linux group
- Remove a user from Linux group
- Delete or Remove a Linux group
- Users and groups
- Overview
- Permissions and ownership
How to Manage Users and Groups in Linux
In this article we are going to learn How we can add/remove/modify users and groups on Linux operating systems using CLI / How to Manage Users and Groups in Linux.
Manage Users and Groups in Linux
What is a Linux user?
A user is an entity, in a Linux operating system, that can manipulate files and perform several other operations.
Types of Linux Users
There are two types of users which exist on a typical Linux operating system.
Linux System users
A system user account is created by the operating system during its installation and is used for operation system defined purposes. They have user id’s predefined (100-999)
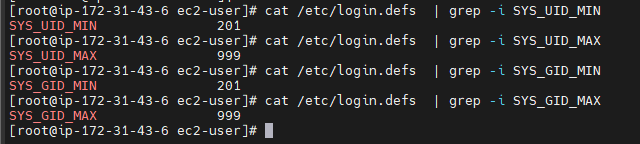
This range can be verified in the file /etc/login.defs
cat /etc/login.defs | grep -i SYS_UID_MIN cat /etc/login.defs | grep -i SYS_UID_MAX cat /etc/login.defs | grep -i SYS_GID_MIN cat /etc/login.defs | grep -i SYS_GID_MAX
Linux Regular users
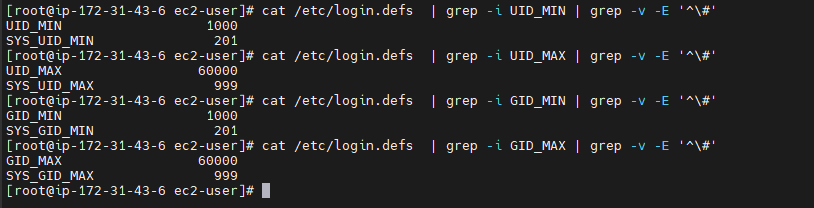
The regular user accounts has ids begin from 1000.
cat /etc/login.defs | grep -i UID_MIN | grep -v -E '^\#' cat /etc/login.defs | grep -i UID_MAX | grep -v -E '^\#' cat /etc/login.defs | grep -i GID_MIN | grep -v -E '^\#' cat /etc/login.defs | grep -i GID_MAX | grep -v -E '^\#'
Linux user Accounts:
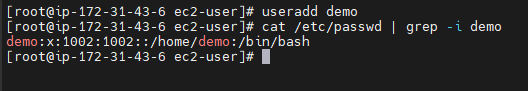
When we create a local user account, users login information and all other details are stored in the /etc/passwd file.
username:password:UID:GID:name:home directory:shell
Following are the commonly used options.
-b : The default base directory for the system.
-c: Adds description/comment to a user account.
-d: The new user will be created using HOME_DIR as the value for the users login directory.
-f: The number of days after a password expires until the account is permanently disabled.
-k: The skeleton directory, which contains files and directories to be copied in the user’s home directory, when the home directory is created by useradd.
-m: Create the user’s home directory if it does not exist. The files and directories contained in the skeleton directory will be copied to the home directory.
-M: Do not create the user’s home directory, even if the system wide setting from /etc/login.defs (CREATE_HOME) is set to yes.
-s: The name of the user’s login shell. The default is to leave this field blank, which causes the system to select the default login shell specified by the SHELL variable in /etc/default/useradd, or an empty string by default.
-u: The numerical value of the user’s ID.
-g: The group name or number of the user’s initial login group.
-G: Adds the user to multiple groups.
-r: Files in the user’s home directory will be removed along with the home directory itself and the user’s mail spool.
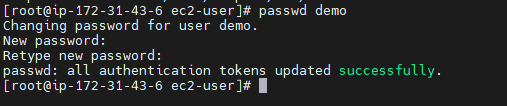
Assign Password to a Linux user
Using the below command we can assign passwords to linux users.
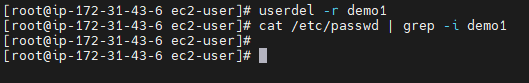
Delete Linux user
Using the below command you can delete a user from the Linux operating system.
Modifying users properties in Linux
Following commands are used to modify an existing user’s properties.
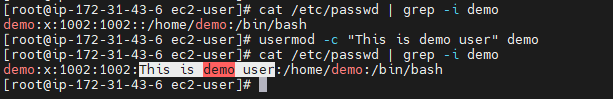
Update the comment part
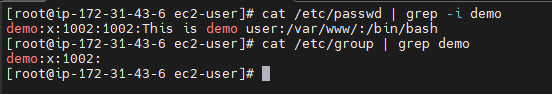
usermod -c “This is demo user” demo
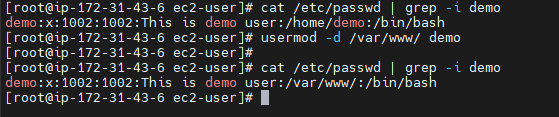
Change User Home Directory
Setting User Account Expiry Date
usermod -e 2022-11-05 demo chage -l demo
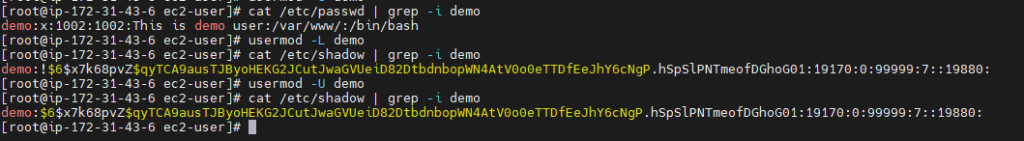
Lock and unlock the user account
Use ‘-L’ (lock) option with usermod command to lock the user account and to unlock use -U option.
Once locked, the user can’t login by using the password and you will see a ! added before the encrypted password in /etc/shadow file, meaning the password is disabled.
usermod -L demo usermod -U demo Group Management
There are two types of groups in Linux. The primary group and secondary group. On Linux when you create a user the primary group that the user belongs to also gets created with the same name as the user.
You can see in the above image that the demo user is part of its own primary group named demo.
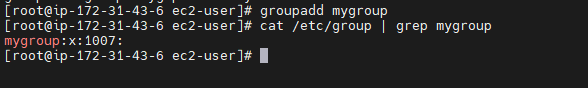
Create a Linux Group
Use below command to create a linux group
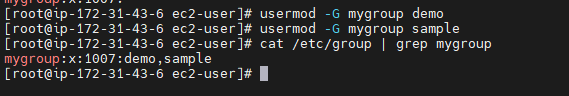
Add users to a Linux group
We can add users to become part of any other groups
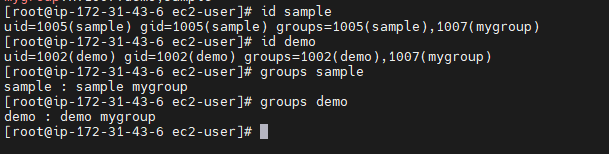
usermod -G mygroup demo usermod -G mygroup sampleNow another way to check group information of a Linux user using id and groups command
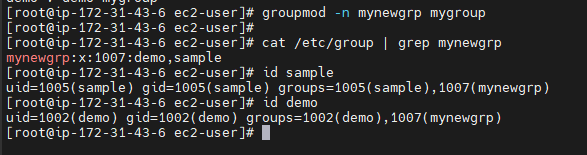
id demo id sample groups demo groups sample Change name of a Linux group
Use below command to change name of linux group
groupmod -n newname oldname
groupmod -n mynewgrp mygroup
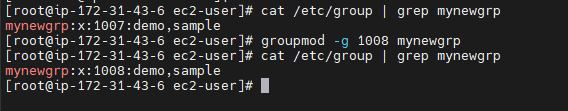
Change GID of a Linux group
Use below command to change GID of linux group
groupmod -g newgid groupname
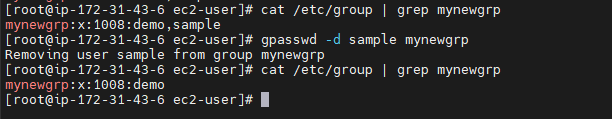
Remove a user from Linux group
Use below commands to remove a user from Linux group
gpasswd -d sample mynewgrp
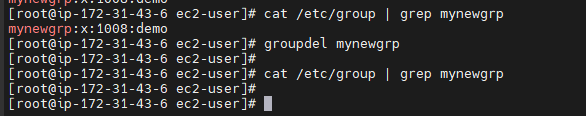
Delete or Remove a Linux group
Use below command to delete or remove linux group
We have covered Manage User and Groups in Linux
How we can add/remove/modify users and groups on Linux operating systems using CLI / How to Manage Users and Groups in Linux.
Related Articles:
Users and groups
Users and groups are used on GNU/Linux for access control—that is, to control access to the system’s files, directories, and peripherals. Linux offers relatively simple/coarse access control mechanisms by default. For more advanced options, see ACL, Capabilities and PAM#Configuration How-Tos.
Overview
A user is anyone who uses a computer. In this case, we are describing the names which represent those users. It may be Mary or Bill, and they may use the names Dragonlady or Pirate in place of their real name. All that matters is that the computer has a name for each account it creates, and it is this name by which a person gains access to use the computer. Some system services also run using restricted or privileged user accounts.
Managing users is done for the purpose of security by limiting access in certain specific ways. The superuser (root) has complete access to the operating system and its configuration; it is intended for administrative use only. Unprivileged users can use several programs for controlled privilege elevation.
Any individual may have more than one account as long as they use a different name for each account they create. Further, there are some reserved names which may not be used such as «root».
Users may be grouped together into a «group», and users may be added to an existing group to utilize the privileged access it grants.
Note: The beginner should use these tools carefully and stay away from having anything to do with any other existing user account, other than their own.
Permissions and ownership
The UNIX operating system crystallizes a couple of unifying ideas and concepts that shaped its design, user interface, culture and evolution. One of the most important of these is probably the mantra: «everything is a file,» widely regarded as one of the defining points of UNIX. This key design principle consists of providing a unified paradigm for accessing a wide range of input/output resources: documents, directories, hard-drives, CD-ROMs, modems, keyboards, printers, monitors, terminals and even some inter-process and network communications. The trick is to provide a common abstraction for all of these resources, each of which the UNIX fathers called a «file.» Since every «file» is exposed through the same API, you can use the same set of basic commands to read/write to a disk, keyboard, document or network device.
A fundamental and very powerful, consistent abstraction provided in UNIX and compatible operating systems is the file abstraction. Many OS services and device interfaces are implemented to provide a file or file system metaphor to applications. This enables new uses for, and greatly increases the power of, existing applications — simple tools designed with specific uses in mind can, with UNIX file abstractions, be used in novel ways. A simple tool, such as cat, designed to read one or more files and output the contents to standard output, can be used to read from I/O devices through special device files, typically found under the /dev directory. On many systems, audio recording and playback can be done simply with the commands, » cat /dev/audio > myfile » and » cat myfile > /dev/audio ,» respectively.
Every file on a GNU/Linux system is owned by a user and a group. In addition, there are three types of access permissions: read, write, and execute. Different access permissions can be applied to a file’s owning user, owning group, and others (those without ownership). One can determine a file’s owners and permissions by viewing the long listing format of the ls command:
total 13740 drwxr-xr-x 2 root root 4096 Jan 12 00:33 grub -rw-r--r-- 1 root root 8570335 Jan 12 00:33 initramfs-linux-fallback.img -rw-r--r-- 1 root root 1821573 Jan 12 00:31 initramfs-linux.img -rw-r--r-- 1 root root 1457315 Jan 8 08:19 System.map26 -rw-r--r-- 1 root root 2209920 Jan 8 08:19 vmlinuz-linux
The first column displays the file’s permissions (for example, the file initramfs-linux.img has permissions -rw-r—r— ). The third and fourth columns display the file’s owning user and group, respectively. In this example, all files are owned by the root user and the root group.
total 16 drwxrwx--- 1 root vboxsf 16384 Jan 29 11:02 sf_Shared
In this example, the sf_Shared directory is owned by the root user and the vboxsf group. It is also possible to determine a file’s owners and permissions using the stat command: