Using Linux Raw Sockets
In an effort to learn how TCP/IP works, I decided to start playing around with a low-level TCP/IP library, smoltcp. Some of the examples (particularly, the clone of tcpdump ) require using raw sockets, which need to be run as the root user. Running network programs as root is pretty dangerous, and is something that one should probably never do.
In this post, I’ll be discussing how to use raw sockets without having to run the whole program as root. And while the library I’m working with is written in Rust, I’ll be using examples written in C.
Why does it mean to access a raw socket?
Sockets are the means by which programs on Linux way talk to the internet. The socket system call creates a file descriptor that can be written to and read from. The connect system call can then be used to connect the socket to some remote address. After that, writing to the socket sends data to that remote address, while reading from the socket file descriptor reads data sent from the remote address.
There are two main types of sockets, stream sockets, and datagram sockets. I won’t get into the details of these now, but streaming sockets are used for applications that use TCP, while datagram sockets are for applications that use UDP. These are both transport-level protocols that follow the network-level IP protocol.
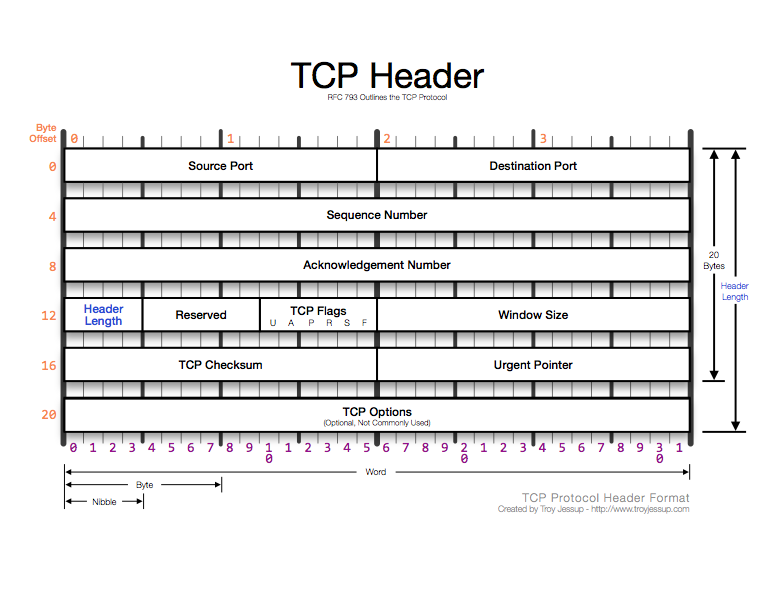
If you are interested in writing your own implementations of one of these protocols, or need to use a different transport-layer protocol, you’ll need to use raw sockets. Raw sockets operate at the network OSI level, which means that transport-level headers such as TCP or UDP headers will not be automatically decoded. If you are implementing a a transport-level protocol, you’ll have to write code to decode and encode the transport-level headers in your application.
Raw Sockets and Security
An important thing worth noting about this is that there is important security-related information stored in TCP and UDP headers:
For instance, the destination port is stored in the TCP headers. This means that packets read from raw sockets don’t have any notion of “port”.
To step back a little bit, an application using TCP or UDP must, when opening up a STREAM or DGRAM socket, declare a port to receive data on. When the application reads data from that socket, they will only see data that was sent to that particular port.
Now, with raw sockets, because network-level IP packets do not have a notion of “port”, all packets coming in over the server’s network device can be read. Applications that open raw sockets have to do the work of filtering out packets that are not relevant themselves, by parsing the TCP headers. The security implications of this are pretty serious–it means that applications with a raw socket open can read any inbound network packets, including those headed to other applications running on the system, which may or may not be run as the same unix user as the application with the raw socket open.
To prevent this from happening, Linux requires that any program that accesses raw sockets be run as root. Actually running network programs as root is dangerous, especially for a sufficiently complicated program, like a TCP implementation.
In this post I’ll cover a couple different strategies for circumventing this.
Attempting to read from a raw socket
To see what happens when we read data from sockets, let’s use this C program that simply sniffs packets entering the system and prints out some information about the packet as an example:
// raw_sock.c #include #include #include #include #include #include int main() // Structs that contain source IP addresses struct sockaddr_in source_socket_address, dest_socket_address; int packet_size; // Allocate string buffer to hold incoming packet data unsigned char *buffer = (unsigned char *)malloc(65536); // Open the raw socket int sock = socket (PF_INET, SOCK_RAW, IPPROTO_TCP); if(sock == -1) //socket creation failed, may be because of non-root privileges perror("Failed to create socket"); exit(1); > while(1) // recvfrom is used to read data from a socket packet_size = recvfrom(sock , buffer , 65536 , 0 , NULL, NULL); if (packet_size == -1) printf("Failed to get packets\n"); return 1; > struct iphdr *ip_packet = (struct iphdr *)buffer; memset(&source_socket_address, 0, sizeof(source_socket_address)); source_socket_address.sin_addr.s_addr = ip_packet->saddr; memset(&dest_socket_address, 0, sizeof(dest_socket_address)); dest_socket_address.sin_addr.s_addr = ip_packet->daddr; printf("Incoming Packet: \n"); printf("Packet Size (bytes): %d\n",ntohs(ip_packet->tot_len)); printf("Source Address: %s\n", (char *)inet_ntoa(source_socket_address.sin_addr)); printf("Destination Address: %s\n", (char *)inet_ntoa(dest_socket_address.sin_addr)); printf("Identification: %d\n\n", ntohs(ip_packet->id)); > return 0; >Compiling this program with:
What is raw socket in linux
NAME
raw - Linux IPv4 raw sockets
SYNOPSIS
#include #include raw_socket = socket(AF_INET, SOCK_RAW, int protocol);
DESCRIPTION
Raw sockets allow new IPv4 protocols to be implemented in user space. A raw socket receives or sends the raw datagram not including link level headers. The IPv4 layer generates an IP header when sending a packet unless the IP_HDRINCL socket option is enabled on the socket. When it is enabled, the packet must contain an IP header. For receiving, the IP header is always included in the packet. In order to create a raw socket, a process must have the CAP_NET_RAW capability in the user namespace that governs its network namespace. All packets or errors matching the protocol number specified for the raw socket are passed to this socket. For a list of the allowed protocols, see the IANA list of assigned protocol numbers at ⟨http://www.iana.org/assignments/protocol-numbers/⟩ and getprotobyname(3). A protocol of IPPROTO_RAW implies enabled IP_HDRINCL and is able to send any IP protocol that is specified in the passed header. Receiving of all IP protocols via IPPROTO_RAW is not possible using raw sockets. ┌───────────────────────────────────────────────────┐ │IP Header fields modified on sending by IP_HDRINCL │ ├──────────────────────┬────────────────────────────┤ │IP Checksum │ Always filled in │ ├──────────────────────┼────────────────────────────┤ │Source Address │ Filled in when zero │ ├──────────────────────┼────────────────────────────┤ │Packet ID │ Filled in when zero │ ├──────────────────────┼────────────────────────────┤ │Total Length │ Always filled in │ └──────────────────────┴────────────────────────────┘ If IP_HDRINCL is specified and the IP header has a nonzero destination address, then the destination address of the socket is used to route the packet. When MSG_DONTROUTE is specified, the destination address should refer to a local interface, otherwise a routing table lookup is done anyway but gatewayed routes are ignored. If IP_HDRINCL isn't set, then IP header options can be set on raw sockets with setsockopt(2); see ip(7) for more information. Starting with Linux 2.2, all IP header fields and options can be set using IP socket options. This means raw sockets are usually needed only for new protocols or protocols with no user interface (like ICMP). When a packet is received, it is passed to any raw sockets which have been bound to its protocol before it is passed to other protocol handlers (e.g., kernel protocol modules). Address format For sending and receiving datagrams (sendto(2), recvfrom(2), and similar), raw sockets use the standard sockaddr_in address structure defined in ip(7). The sin_port field could be used to specify the IP protocol number, but it is ignored for sending in Linux 2.2 and later, and should be always set to 0 (see BUGS). For incoming packets, sin_port is set to zero. Socket options Raw socket options can be set with setsockopt(2) and read with getsockopt(2) by passing the IPPROTO_RAW family flag. ICMP_FILTER Enable a special filter for raw sockets bound to the IPPROTO_ICMP protocol. The value has a bit set for each ICMP message type which should be filtered out. The default is to filter no ICMP messages. In addition, all ip(7) IPPROTO_IP socket options valid for datagram sockets are supported. Error handling Errors originating from the network are passed to the user only when the socket is connected or the IP_RECVERR flag is enabled. For connected sockets, only EMSGSIZE and EPROTO are passed for compatibility. With IP_RECVERR, all network errors are saved in the error queue.
ERRORS
EACCES User tried to send to a broadcast address without having the broadcast flag set on the socket. EFAULT An invalid memory address was supplied. EINVAL Invalid argument. EMSGSIZE Packet too big. Either Path MTU Discovery is enabled (the IP_MTU_DISCOVER socket flag) or the packet size exceeds the maximum allowed IPv4 packet size of 64 kB. EOPNOTSUPP Invalid flag has been passed to a socket call (like MSG_OOB). EPERM The user doesn't have permission to open raw sockets. Only processes with an effective user ID of 0 or the CAP_NET_RAW attribute may do that. EPROTO An ICMP error has arrived reporting a parameter problem.
VERSIONS
IP_RECVERR and ICMP_FILTER are new in Linux 2.2. They are Linux extensions and should not be used in portable programs. Linux 2.0 enabled some bug-to-bug compatibility with BSD in the raw socket code when the SO_BSDCOMPAT socket option was set; since Linux 2.2, this option no longer has that effect.
NOTES
By default, raw sockets do path MTU (Maximum Transmission Unit) discovery. This means the kernel will keep track of the MTU to a specific target IP address and return EMSGSIZE when a raw packet write exceeds it. When this happens, the application should decrease the packet size. Path MTU discovery can be also turned off using the IP_MTU_DISCOVER socket option or the /proc/sys/net/ipv4/ip_no_pmtu_disc file, see ip(7) for details. When turned off, raw sockets will fragment outgoing packets that exceed the interface MTU. However, disabling it is not recommended for performance and reliability reasons. A raw socket can be bound to a specific local address using the bind(2) call. If it isn't bound, all packets with the specified IP protocol are received. In addition, a raw socket can be bound to a specific network device using SO_BINDTODEVICE; see socket(7). An IPPROTO_RAW socket is send only. If you really want to receive all IP packets, use a packet(7) socket with the ETH_P_IP protocol. Note that packet sockets don't reassemble IP fragments, unlike raw sockets. If you want to receive all ICMP packets for a datagram socket, it is often better to use IP_RECVERR on that particular socket; see ip(7). Raw sockets may tap all IP protocols in Linux, even protocols like ICMP or TCP which have a protocol module in the kernel. In this case, the packets are passed to both the kernel module and the raw socket(s). This should not be relied upon in portable programs, many other BSD socket implementation have limitations here. Linux never changes headers passed from the user (except for filling in some zeroed fields as described for IP_HDRINCL). This differs from many other implementations of raw sockets. Raw sockets are generally rather unportable and should be avoided in programs intended to be portable. Sending on raw sockets should take the IP protocol from sin_port; this ability was lost in Linux 2.2. The workaround is to use IP_HDRINCL.
BUGS
SEE ALSO
recvmsg(2), sendmsg(2), capabilities(7), ip(7), socket(7) RFC 1191 for path MTU discovery. RFC 791 and the header file for the IP protocol.
COLOPHON
This page is part of release 5.05 of the Linux man-pages project. A description of the project, information about reporting bugs, and the latest version of this page, can be found at https://www.kernel.org/doc/man-pages/.