- Introduction to BackBox Linux
- It’s standard compliant
- Menu and applications
- Integrated anonymous feature
- RAM wipe
- Full disk encryption
- BackBox Linux for Penetration Testing
- What Makes BackBox Special?
- Installation
- Using BackBox
- The Conclusion
- What linux is backbox
- BackBox Linux
- What is?
- Performance and speed are key elements
- Everything is in the right place
- It’s hacker friendly
Introduction to BackBox Linux
BackBox is a Linux distribution built on thin Ubuntu core. It has been developed to perform penetration tests and security assessments.
Designed to be fast, easy to use and provide a minimal yet complete desktop environment, thanks to its own software repositories, always being updated to the latest stable version of the most used and best known ethical hacking tools.
It’s standard compliant
The software packaging process, the configuration and the tweaking of the system follows up the Ubuntu/Debian standard guide lines.
Any of the Debian and Ubuntu users will feel very comfortable, while newcomers will follow the official documentation and BackBox additions to customize their system without any tricky workaround, because it is standard and straight forward!
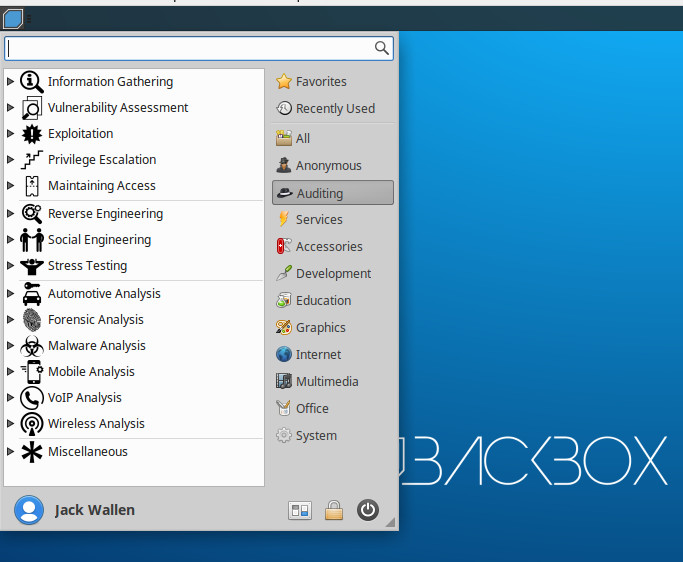
Menu and applications
The main menu is well organized systematically where every tool is placed in it’s appropriate section. The selection of every single tool has been done with accuracy and restricted procedure in order to avoid any redundancy caused by programs having similar functionalities.
With a particular attention to the end user needs, all menus and configuration files have been organized and reduced to the bare minimum in order to provide an intuitive and user friendly GNU/Linux distro.
Integrated anonymous feature
The anonymous mode with transparent Tor proxy strongly protects your privacy!
MAC address and the hostname is randomly being changed and this makes the system not traceable within the LAN . Integration of BleachBit for the cleaning and automation of the logs provides an extra security level.
RAM wipe
RAM wipe is the feature that allows you to make sure that nobody could compromise your privacy and it protects your system against the memory recovery!
RAM Wiping at shutdown/reboot keeps your system safe against similar attacks
Full disk encryption
Full Hard Disk encryption in the installation fase by using LUKS on LVM
what-is-backbox-linux.txt · Last modified: 2015/10/30 15:53 by ostendali
BackBox Linux for Penetration Testing
Any given task can succeed or fail depending upon the tools at hand. For security engineers in particular, building just the right toolkit can make life exponentially easier. Luckily, with open source, you have a wide range of applications and environments at your disposal, ranging from simple commands to complicated and integrated tools.
The problem with the piecemeal approach, however, is that you might wind up missing out on something that can make or break a job… or you waste a lot of time hunting down the right tools for the job. To that end, it’s always good to consider an operating system geared specifically for penetration testing (aka pentesting).
Within the world of open source, the most popular pentesting distribution is Kali Linux . It is, however, not the only tool in the shop. In fact, there’s another flavor of Linux, aimed specifically at pentesting, called BackBox . BackBox is based on Ubuntu Linux, which also means you have easy access to a host of other outstanding applications besides those that are included, out of the box.
What Makes BackBox Special?
BackBox includes a suite of ethical hacking tools, geared specifically toward pentesting. These testing tools include the likes of:
- Web application analysis
- Exploitation testing
- Network analysis
- Stress testing
- Privilege escalation
- Vulnerability assessment
- Computer forensic analysis and exploitation
- And much more
Out of the box, one of the most significant differences between Kali Linux and BackBox is the number of installed tools. Whereas Kali Linux ships with hundreds of tools pre-installed, BackBox significantly limits that number to around 70. Nonetheless, BackBox includes many of the tools necessary to get the job done, such as:
- Ettercap
- Msfconsole
- Wireshark
- ZAP
- Zenmap
- BeEF Browser Exploitation
- Sqlmap
- Driftnet
- Tcpdump
- Cryptcat
- Weevely
- Siege
- Autopsy
BackBox is in active development, the latest version (5.3) was released February 18, 2019. But how is BackBox as a usable tool? Let’s install and find out.
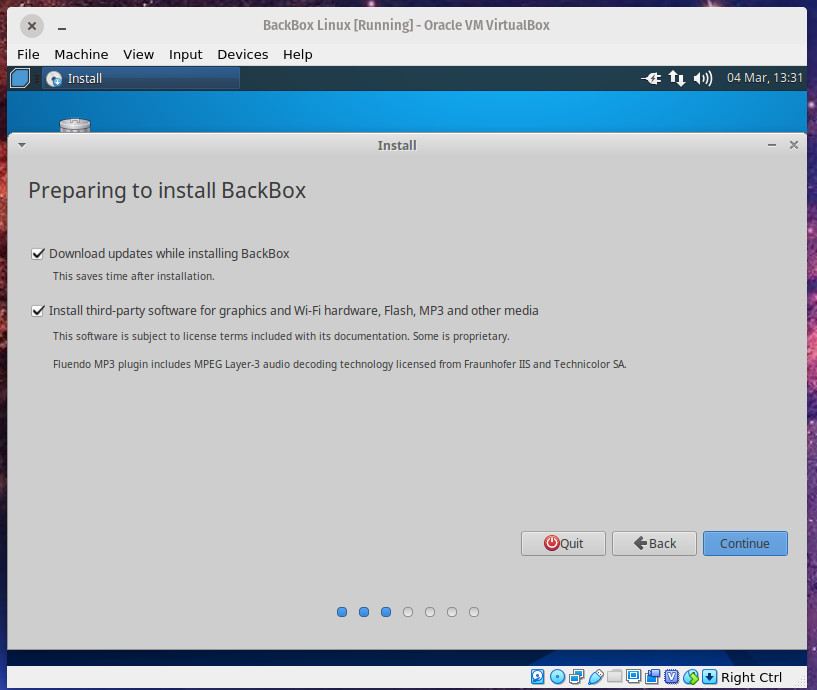
Installation
If you’ve installed one Linux distribution, you’ve installed them all … with only slight variation. BackBox is pretty much the same as any other installation. Download the ISO , burn the ISO onto a USB drive, boot from the USB drive, and click the Install icon.
The installer ( Figure 1 ) will be instantly familiar to anyone who has installed a Ubuntu or Debian derivative. Just because BackBox is a distribution geared specifically toward security administrators, doesn’t mean the operating system is a challenge to get up and running. In fact, BackBox is a point-and-click affair that anyone, regardless of skills, can install.
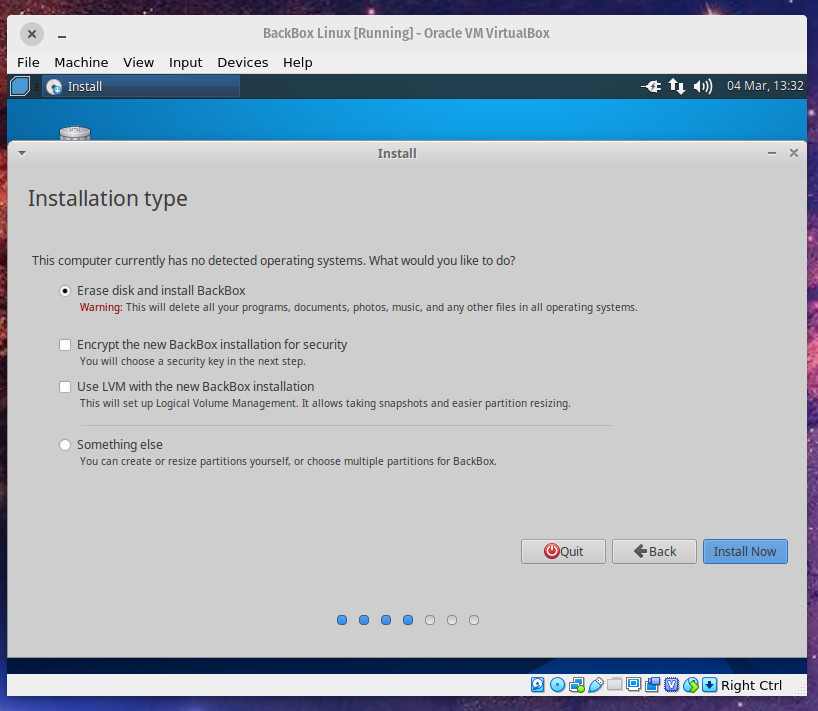
The trickiest section of the installation is the Installation Type. As you can see ( Figure 2 ), even this step is quite simple.
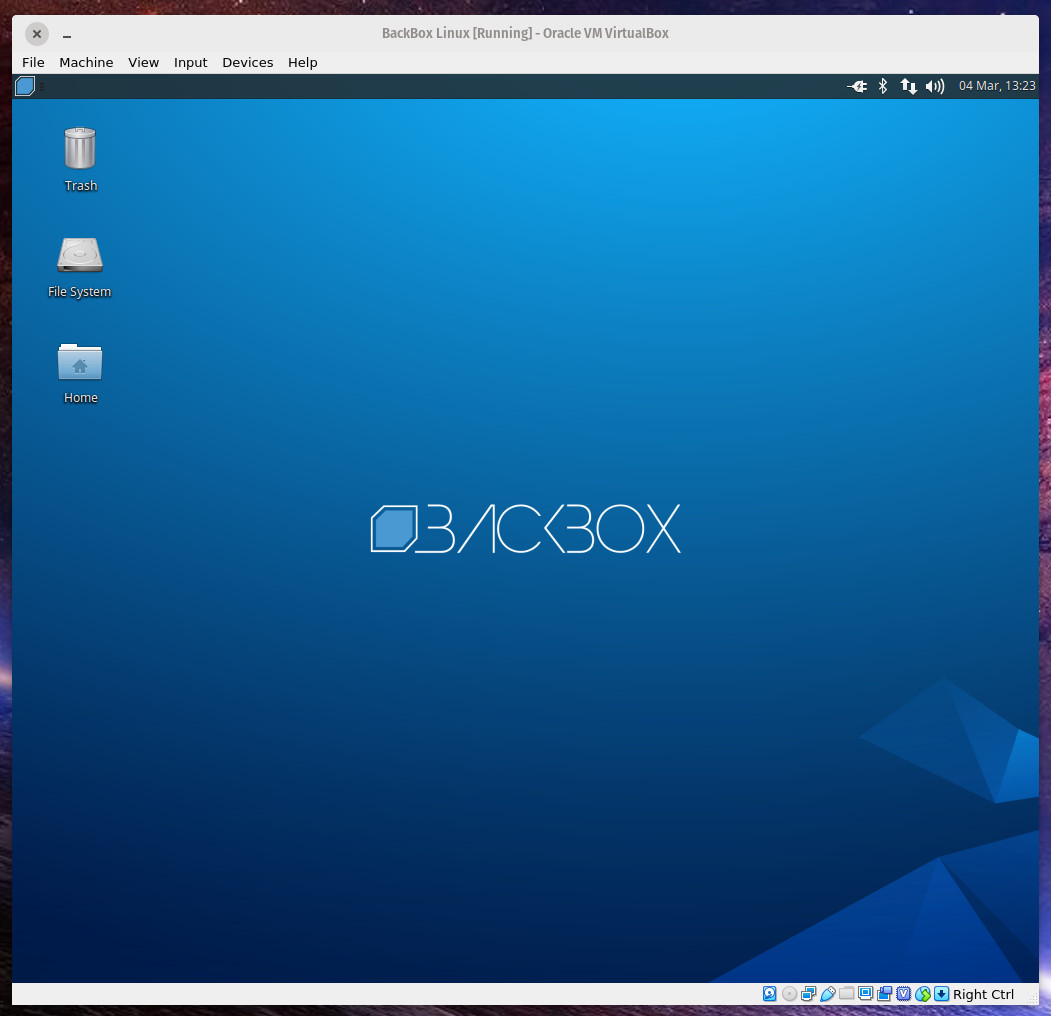
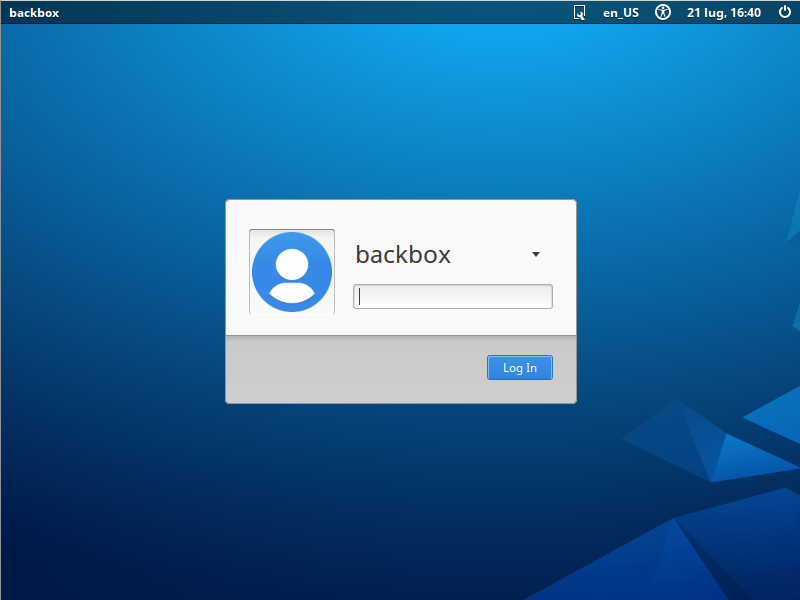
Once you’ve installed BackBox, reboot the system, remove the USB drive, and wait for it to land on the login screen. Log into the desktop and you’re ready to go ( Figure 3 ).
Using BackBox
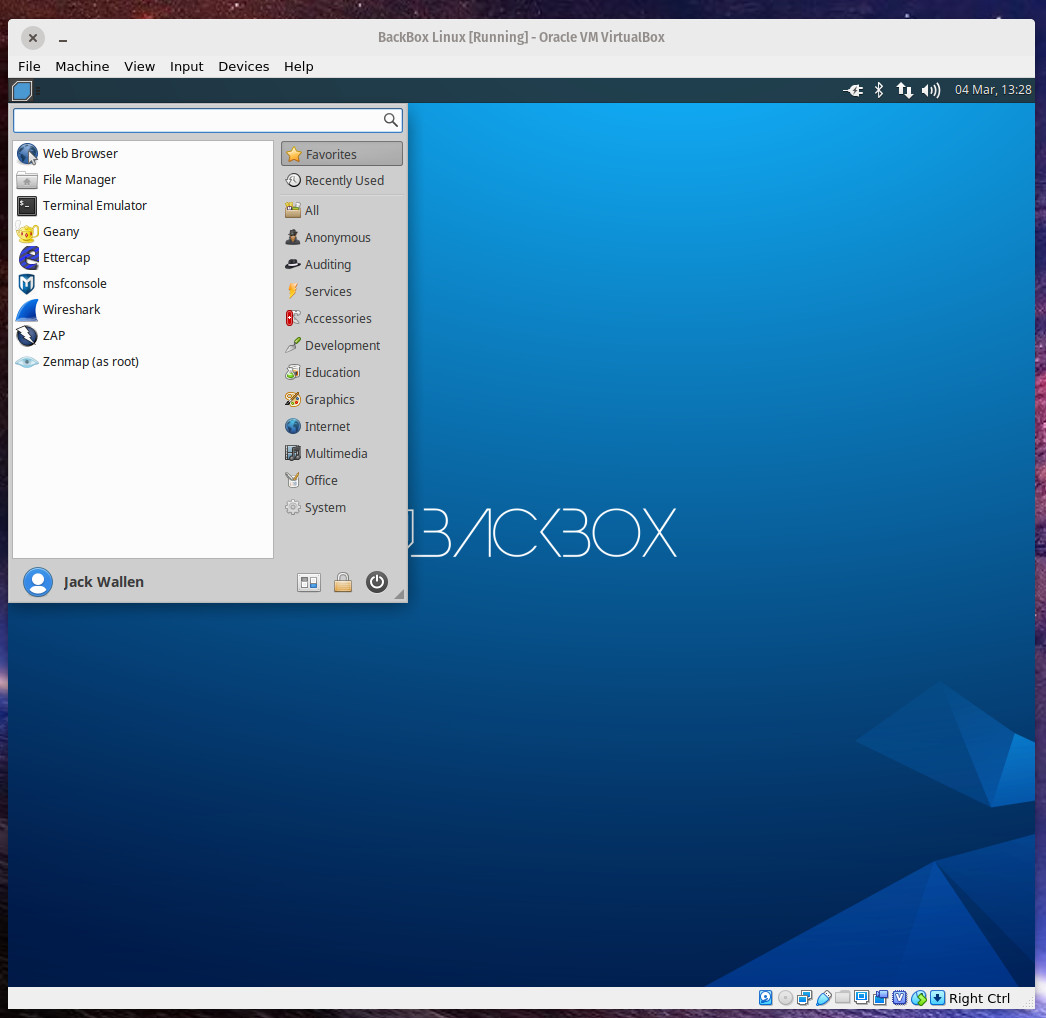
Thanks to the Xfce desktop environment , BackBox is easy enough for a Linux newbie to navigate. Click on the menu button in the top left corner to reveal the menu ( Figure 4 ).
From the desktop menu, click on any one of the favorites (in the left pane) or click on a category to reveal the related tools ( Figure 5 ).
The menu entries you’ll most likely be interested in are:
- Anonymous – allows you to start an anonymous networking session.
- Auditing – the majority of the pentesting tools are found in here.
- Services – allows you to start/stop services such as Apache, Bluetooth, Logkeys, Networking, Polipo, SSH, and Tor.
Before you run any of the testing tools, I would recommend you first making sure to update and upgrade BackBox. This can be done via a GUI or the command line. If you opt to go the GUI route, click on the desktop menu, click System, and click Software Updater. When the updater completes its check for updates, it will prompt you if any are available, or if (after an upgrade) a reboot is necessary ( Figure 6 ).
Should you opt to go the manual route, open a terminal window and issue the following two commands:
sudo apt-get update sudo apt-get upgrade -y
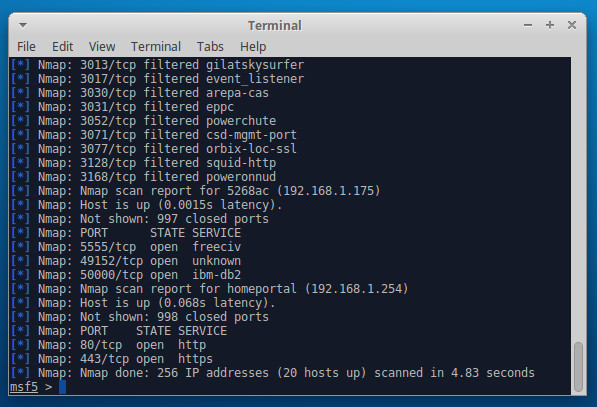
Many of the BackBox pentesting tools do require a solid understanding of how each tool works, so before you attempt to use any given tool, make sure you know how to use said tool. Some tools (such as Metasploit) are made a bit easier to work with, thanks to BackBox. To run Metasploit, click on the desktop menu button and click msfconsole from the favorites (left pane). When the tool opens for the first time, you’ll be asked to configure a few options. Simply select each default given by clicking your keyboard Enter key when prompted. Once you see the Metasploit prompt, you can run commands like:
The above command will list out all discovered ports on a 192.168.1.x network scheme ( Figure 7 ).
Even often-challenging tools like Metasploit are made far easier than they are with other distributions (partially because you don’t have to bother with installing the tools). That alone is worth the price of entry for BackBox (which is, of course, free).
The Conclusion
Although BackBox usage may not be as widespread as Kali Linux, it still deserves your attention. For anyone looking to do pentesting on their various environments, BackBox makes the task far easier than so many other operating systems. Give this Linux distribution a go and see if it doesn’t aid you in your journey to security nirvana.
What linux is backbox

BackBox Linux
Penetration Testing Distribution
What is?
BackBox Linux is a penetration testing and security assessment oriented Linux distribution providing a network and systems analysis toolkit. It includes some of the most commonly known/used security and analysis tools, aiming for a wide spread of goals, ranging from web application analysis to network analysis, stress tests, sniffing, vulnerability assessment, computer forensic analysis, automotive and exploitation. It has been built on Ubuntu core system yet fully customized, designed to be one of the best Penetration testing and security distribution and more.
Performance and speed are key elements
Starting from an appropriately configured XFCE desktop manager it offers stability and the speed, that only a few other DMs can offer, reaching in extreme tweaking of services, configurations, boot parameters and the entire infrastructure. BackBox has been designed with the aim of achieving the maximum performance and minimum consumption of resources. This makes BackBox a very fast distro and suitable even for old hardware configurations.
Everything is in the right place
The main menu of BackBox has been well organized and designed to avoid any chaos/mess finding tools that we are looking for. The selection of every single tool has been done with accuracy in order to avoid any redundancies and the tools that have similar functionalities. With particular attention to the end user every needs, all menu and configuration files are have been organized and reduced to a minimum essential, necessary to provide an intuitive, friendly and easy usage of Linux distributiont.
It’s hacker friendly
The software packaging process, the configuration and the tweaking of the system follows up the Ubuntu/Debian standard guide lines. If you’d like to make any change/modification, in order to suite to your purposes, or maybe add additional tools that is not present in the repositories, nothing could be easier in doing that with BackBox. Create your own Launchpad PPA, send your package to dev team and contribute actively to the evolution of BackBox Linux.