- How to hack Wi-Fi in Windows
- New Router Scan by Stas’M features
- Download the latest Router Scan
- What do I need to use the wireless audit capabilities of Router Scan?
- Overview of wireless networks in Router Scan
- Getting a WPA password based on the predicted WPS PIN in Router Scan
- Brute-force password from any Wi-Fi network with Router Scan
- View passwords from Wi-Fi to which the computer was previously connected
- How to determine the location of Wi-Fi
- Problem solving
- 1. Endless error “Association failed”
- 2. The Wireless Networks tab does not work on Linux
- 3. Npcap is installed, but still the error “Please install WinPcap and try again”
- 4. Wireless attacks do not work in Router Scan
- Conclusion
- Related articles:
How to hack Wi-Fi in Windows
There are not any free Windows-based tools for wireless audit, are there?
Router Scan – free Windows program with GUI to scan networks and hack routers – got new amazing features. Now you can perform Wi-Fi security audit from Windows.
New Router Scan by Stas’M features
In Router Scan since v2.60, wireless audit capabilities have been implemented, they include brute-force attack against WPA/WPA2 key of a network, obtaining a password using the WPS PIN, and Pixie Dust attack.
Download the latest Router Scan
Go to the program page and click the Mirror download button:
Unzip the archive and run the RouterScan.exe file.
What do I need to use the wireless audit capabilities of Router Scan?
If you see error messages when trying to use the wireless audit functions:
[-] Raw packet capture not available. [*] Please install WinPcap and try again.
Then you need to install WinPcap, a link to download (choose the version for Windows): https://www.winpcap.org/install/default.htm
Then you need to install Npcap, link to the official page where you will find the installer: https://nmap.org/npcap/. When installing Npcap, be sure to check the “Install Npcap in WinPcap API-compatible mode” checkbox!

To brute-force WPA-PSK key (in other words, the password from the Wi-Fi network), any Wi-Fi card should approach, since the Router Scan just try to connect using different passwords in ordinary way. If you have several wireless dongles you should give preference to one that sees more networks and keeps the signal better.
In the attacks on the WPS PIN when using Alfa AWUS036NHA I received an error message:
[-] Failed to start raw packet capture. [-] Try updating your Wi-Fi driver and/or installing Npcap in WinPcap-compatible mode.
Since my second Alfa AWUS052NH adapter works with Router Scan fine, it is more long-range, and I mostly use it, including Linux, I did not try to cope my issues with AWUS036NHA. Perhaps the problem could be solved in the recommended way. By the way, write in the comments, what wireless adapters work with Router Scan well, and with what problems you occurred.
Since WinPcap also contains the driver, I would not be surprised if even wireless cards that are unsuitable for use in Wi-Fi auditing in Linux due to driver limitations are suitable for WPS PIN attacks in Windows. I cannot verify this, because at hand there is no ‘usual’ Wi-Fi adapter.
Built-in Wi-Fi adatper Intel Corporation Centrino Advanced-N 6235 (rev 24) (in Linux it supports monitor mode and injection) also works well with Router Scan.
Configuring Router Scan
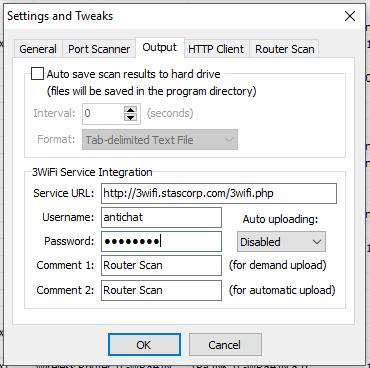
For some of our attacks, we need information from 3WiFi. Guest access is enough for our needs. Go to the Router Scan settings and enter «antichat» as Username and Password:
Overview of wireless networks in Router Scan
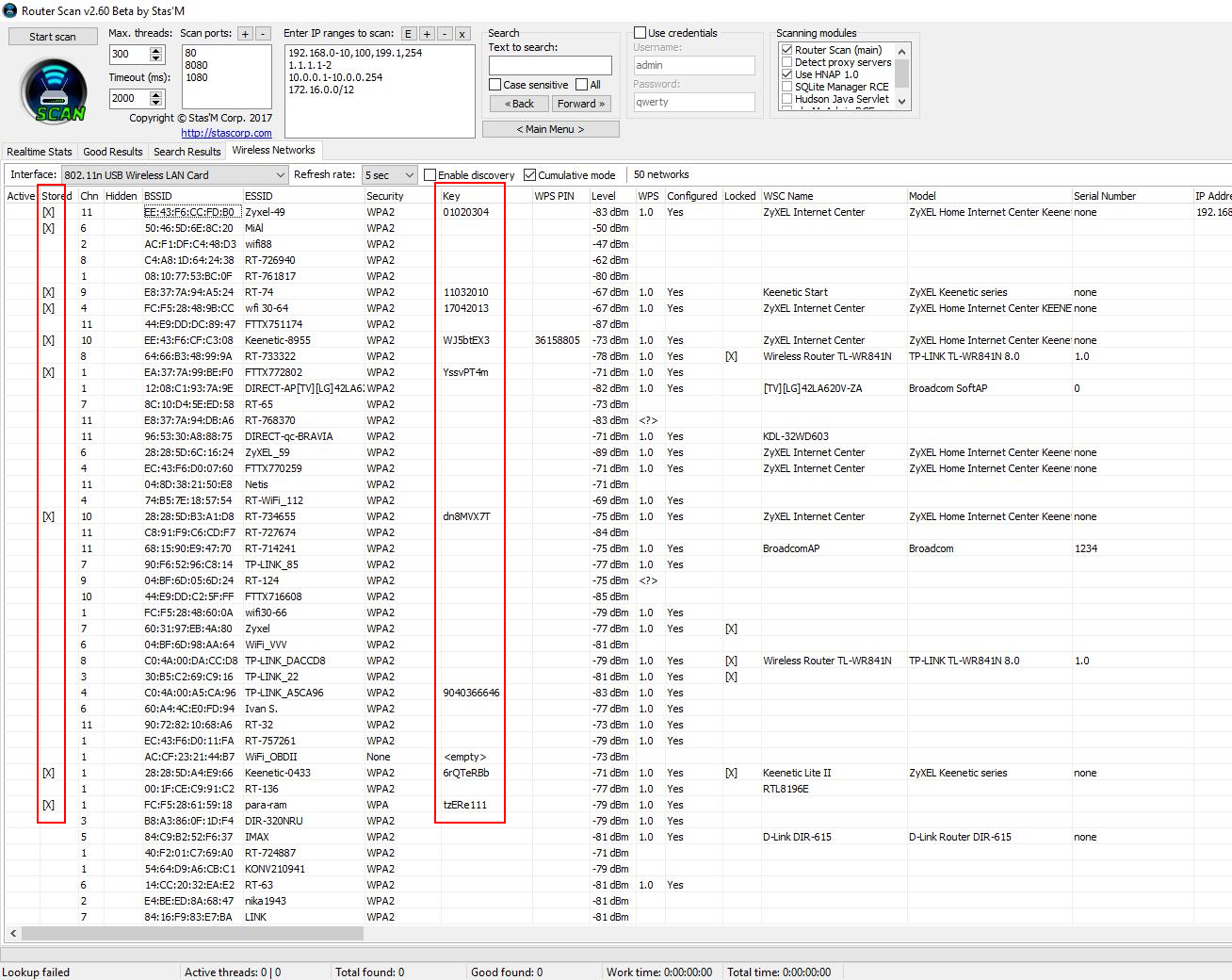
In Router Scan, since version v2.60, the Wireless Networks tab has appeared:
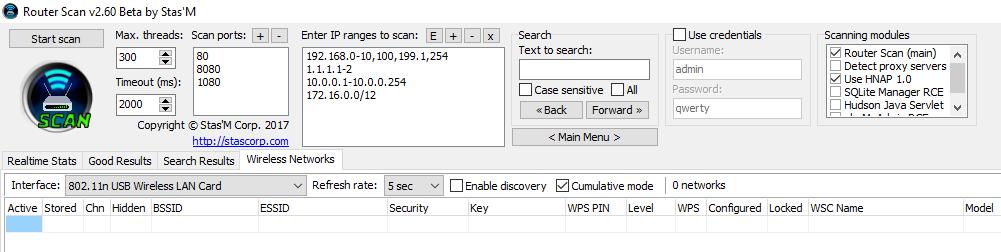
In the Interface field, select the Wi-Fi adaper that you want to use for auditing Wi-Fi networks. If you check Enable discovery, data will be collected about available access points within reach. To prevent access points from disappearing from the list, tick the Cumulative mode:
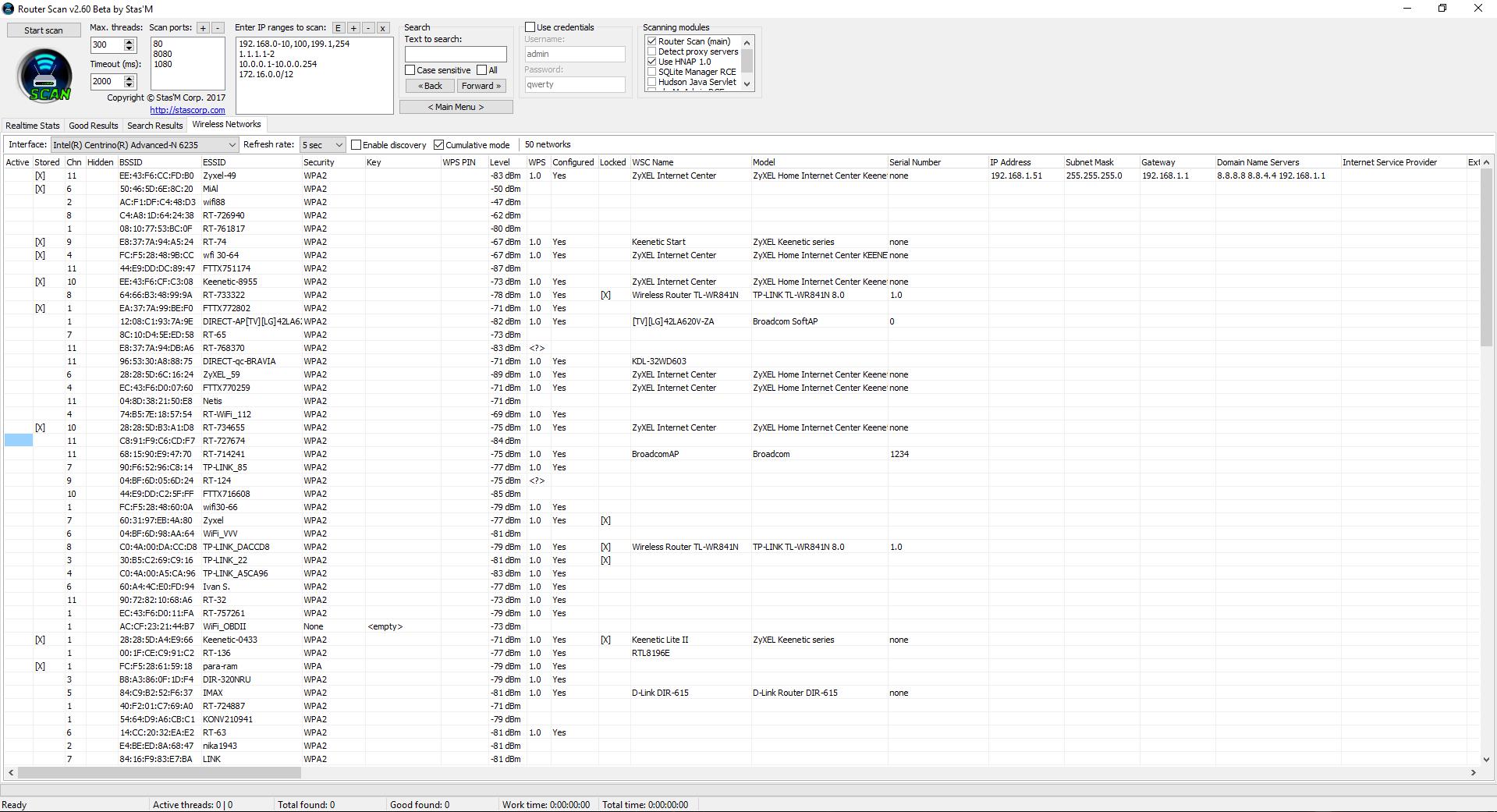
The Active column marks (seemingly) the networks to which you are currently connected.
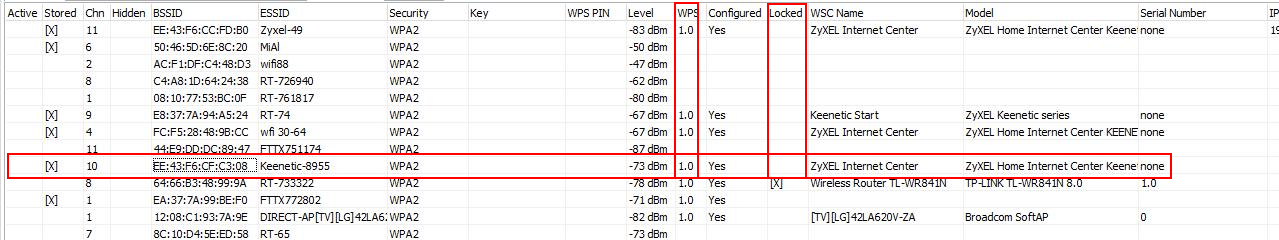
Please note that we have access to advanced information about access points. You can see the exact model (WSC Name and Model fields) for the AP with WPS.
Getting a WPA password based on the predicted WPS PIN in Router Scan
In one of my articles entitled ‘Effective WPS PINs attack based on known PIN and PIN generation algorithms’, I talked about this method of fast Wi-Fi hacking, when WPS PIN is calculated on the basis of algorithms, or taken from the database. If the PIN is guessed, then the password from the Wi-Fi network is revealed.
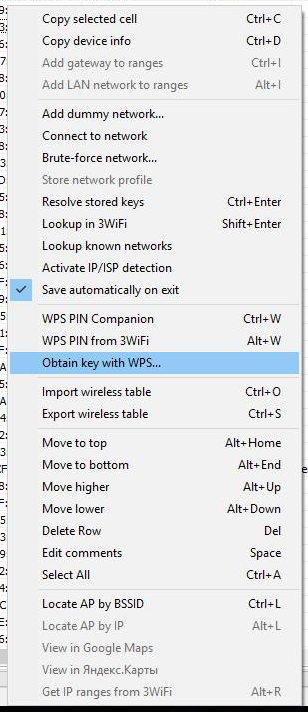
Approximately the same attack is implemented in Router Scan. The program contains the WPS PIN Companion tool. This tool ‘guesses’ the WPS PIN of the wireless network. The PIN is calculated by certain algorithms, based on the MAC-address and serial number of the router (only for some generation algorithms). In the new version WPS PIN Companion received new algorithms and other improvements, but the main thing is its combination with another tool, which in the context menu (called by the right mouse button) is named Obtain key with WPS …:
Since only access points with WPS are suitable for hacking, it is necessary to select those with a version number in the WPS column, and nothing is written in the Locked column (i.e. WPS for this AP should not be blocked), an example of an appropriate point access:
Click on the selected AP with the right mouse button, select Obtain key with WPS …:

If you already have a WPS PIN (or several pins), enter them in the PINs field. If you do not have a pin, then close this window.
Two options are also available in the context menu:
The first calculates the PIN for a given access point by algorithms:
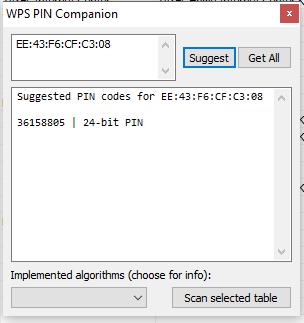
As you can see, the guessed pin is 36158805.
When you click on WPS PIN from 3WiFi, the following window is displayed to us:
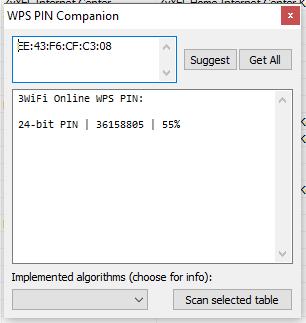
In it again 36158805 and, apparently, the percentages of coincidence.
Let’s return to the option Obtain key with WPS …:
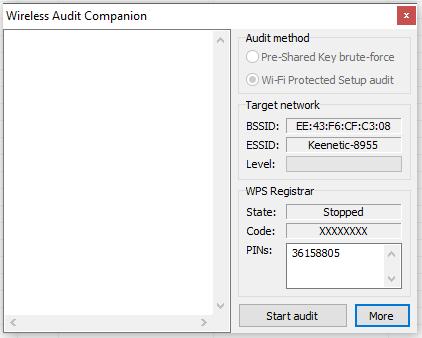
Our pin is entered automatically, press Start audit.
As you can see, the password is successfully cracked:
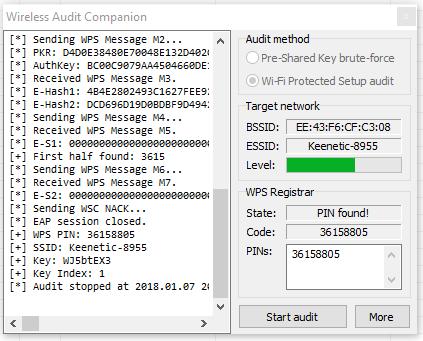
This is indicated by the lines:
[+] WPS PIN: 36158805 [+] SSID: Keenetic-8955 [+] Key: WJ5btEX3
The password from Wi-Fi is WJ5btEX3.
Brute-force password from any Wi-Fi network with Router Scan
The previous method is fast, but works only for networks with unlocked WPS.
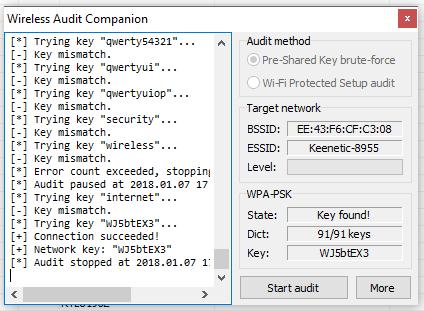
For all other access points, a more universal but slower method is available. Its essence lies in the fact that Router Scan tries to connect to the Wi-Fi network with a password that it takes from the dictionary. If the connection was successful, then the password is guessed, if the connection did fail, then the program proceeds to the next password and tries it, etc. Next, until the password is cracked or the dictionary is completed. Every attempt takes a few seconds — it’s slow.
To start the attack, right-click on the access point of interest to you and select Brute-force network …:

The attack must begin with the selection of the dictionary file. To do this, opposite the Dict field, click (click to load) and select the dictionary file. With the program comes a small dictionary (file wlanpass.txt) for 90 words. You can use it.
Successful password cracking:
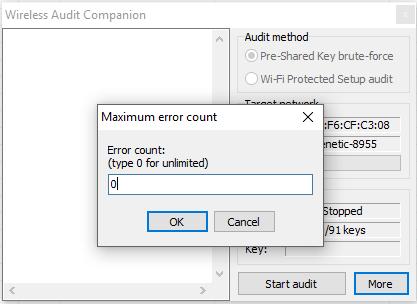
By the way, so that attempts do not stop, click on More, then Maximum error counts and enter 0 for unlimited attempts:
View passwords from Wi-Fi to which the computer was previously connected
Router Scan allows you to get the passwords from the networks you was previously connected to. To do this, select the Resolve stored keys option from the context menu:
How to determine the location of Wi-Fi
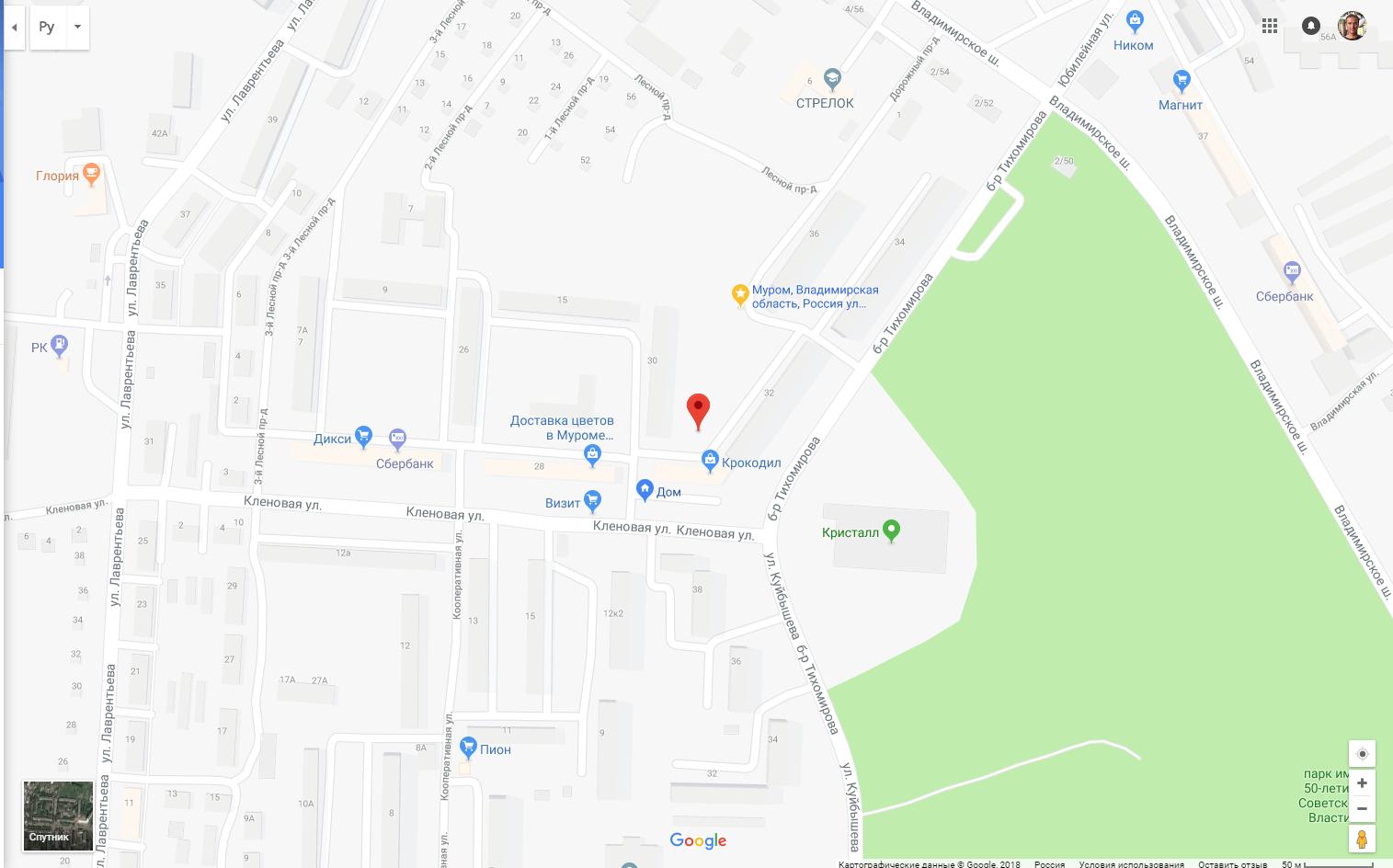
To do this, in the Router Scan select the Locate AP by BSSID option, the following window will appear:
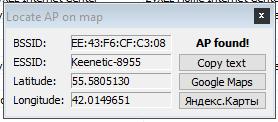
For example, click on Google Maps:
Problem solving
1. Endless error “Association failed”
Sometimes when I attacked Wi-Fi, there were endless messages:
[*] Associating with AP. [-] Association failed. [*] Associating with AP. [-] Association failed.
If you stop and restart the attack, this error usually disappears.
The Wireless Networks tab does not work on Linux.
2. The Wireless Networks tab does not work on Linux
The Wireless Networks tab does not and will never work on Linux, as this functionality in Router Scan requires WinPcap or Npcap, which are not available on Linux.
3. Npcap is installed, but still the error “Please install WinPcap and try again”
If you’ve already installed Npcap or installed Wireshark, but still get the error:
[-] Raw packet capture not available. [*] Please install WinPcap and try again.
The reason may be that you forgot to enable the “Install Npcap in WinPcap API-compatible mode” checkbox. Restart the Npcap installer and enable this option.
4. Wireless attacks do not work in Router Scan
If your Router Scan wireless attacks stopped working, there is now a fix.
Router Scan relies heavily on WinPcap/Npcap for wireless attacks. In the Npcap changelog (https://github.com/nmap/npcap/blob/master/CHANGELOG.md) we can see the following:
Restore raw WiFi frame capture support, which had been broken in a few ways since Npcap 0.9983. Additional improvements enable PacketSetMonitorMode() for non-admin-privileged processes, allowing Wireshark to correctly enable monitor mode via checkbox without requiring WlanHelper.exe.
In short, the functionality associated with wireless attacks has long been broken. Now they fixed it – I checked, the attack on WPS was successful.
So just update Npcap to the latest version. Alternatively, install the latest version of Wireshark – Npcap comes with it.
Conclusion
Router Scan Stas’M is a unique and easy to use program, it has no analogues for either Windows or Linux. New Router Scan features in many ways are also unique for Windows. However, Linux OS can offer additional tools for attacks on the Wi-Fi network.